Microsoft have pushed out a number of updates in their April 2026 release, and one of them has been a long time coming – An update to how Windows handles RDP connectivity The main change for thi...
For four decades, the Border Gateway Protocol (BGP) has functioned as the glue holding the internet together. It was designed to route packets between thousands of networks on the internet (A.K.A. Aut...
Security researchers at Black Lotus Labs have uncovered a sophisticated new malware called “KadNap” that has secretly hijacked over 14,000 devices worldwide to create a massive botnet. If ...
The impending reality of quantum computing poses a significant threat to the cryptographic standards that secure the Internet today. To stay ahead of this threat, the developers of Google Chrome have ...
Most people who use a guest Wi-Fi network, such as the one in a hotel, or the local coffee shop assume that their device and communications are secure, and for a number of years this has been the case...
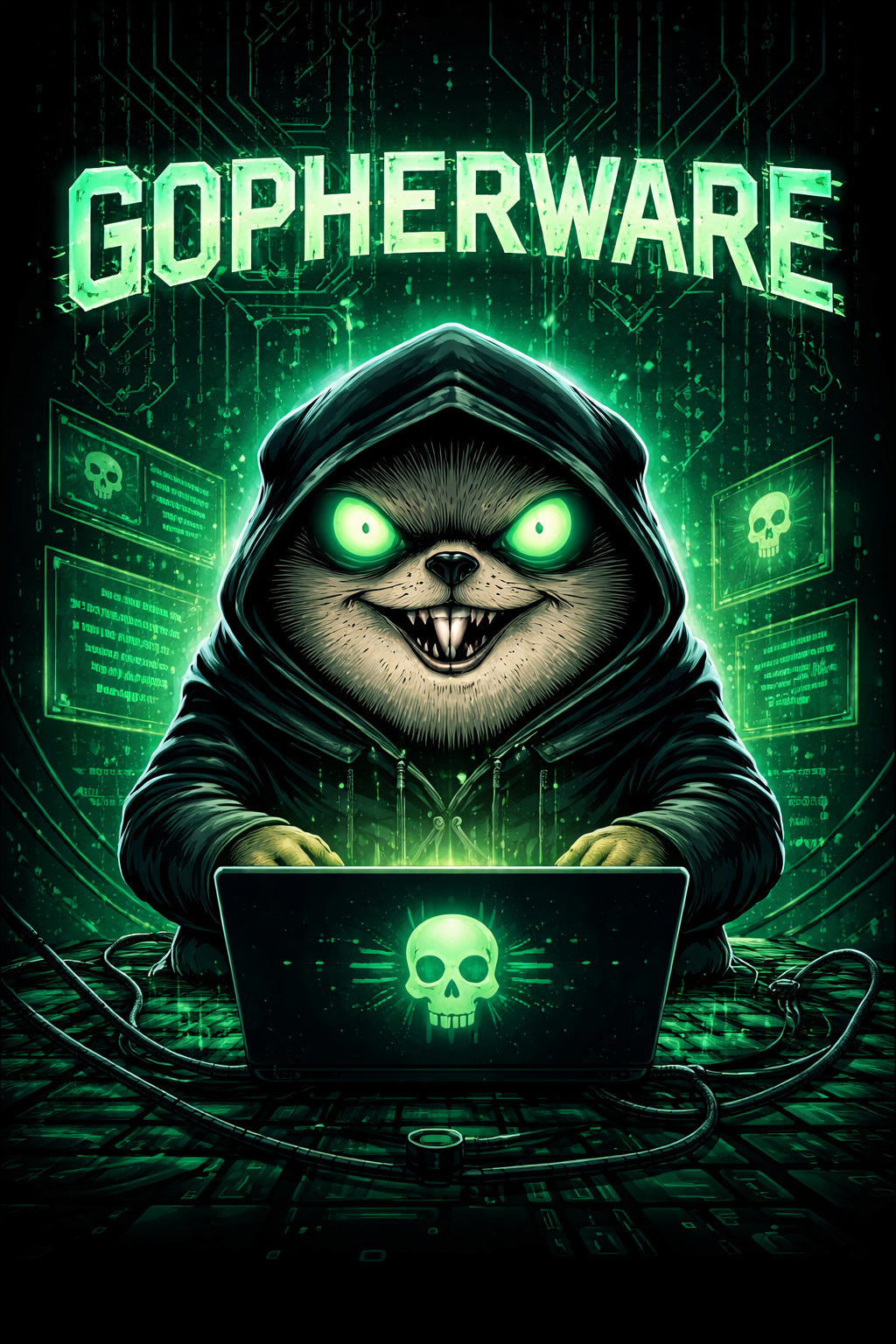
Gopherware (Gopher malware) is the term given to malware written in the Go (Golang) programming language. As a threat, gopherware has seen a massive surge in adoption by threat actors since early 2019...
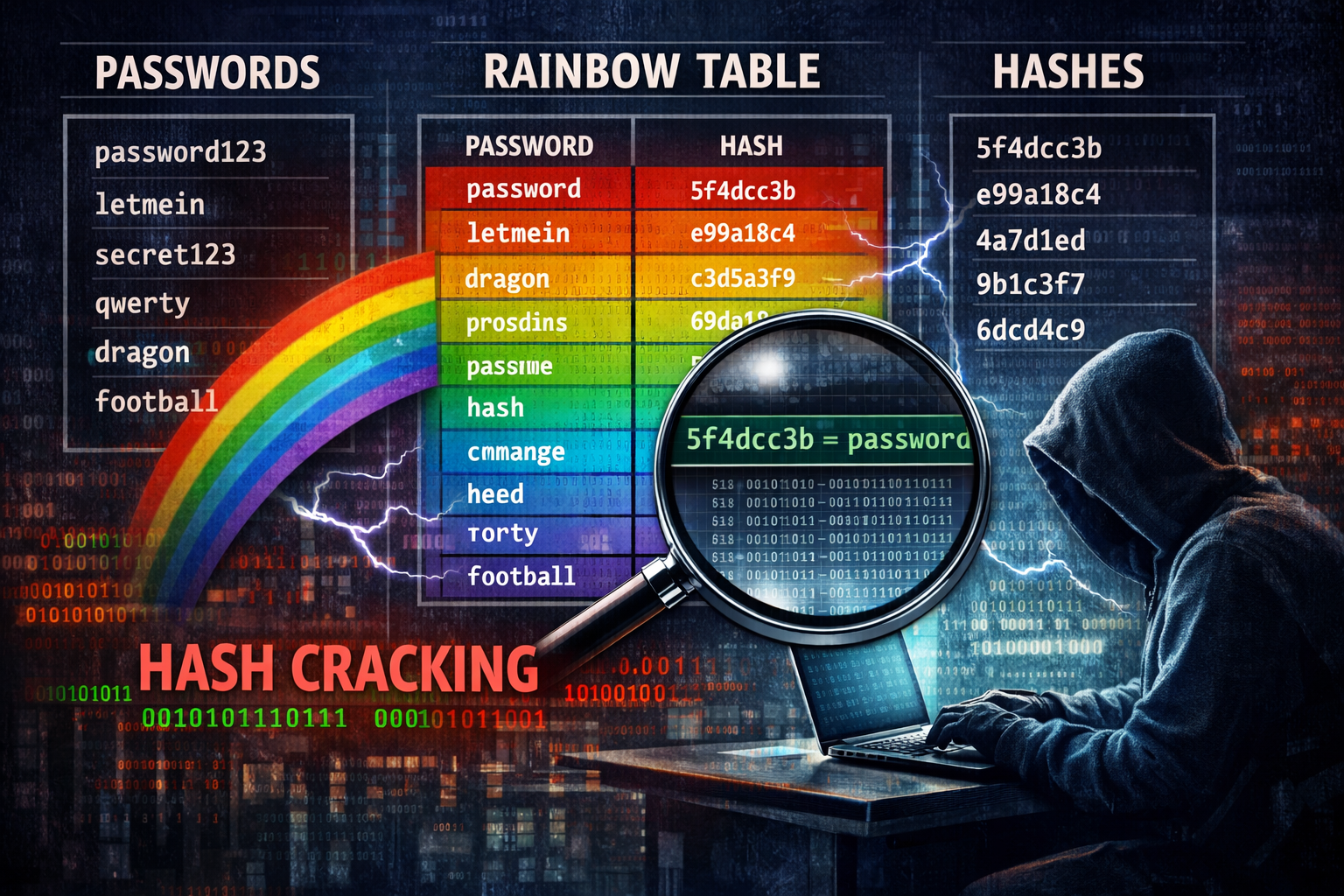
Mandiant (the Google-owned Cyber Security research company) has released a comprehensive dataset of Net-NTLMv1 rainbow tables in an attempt to force organisations to migrate away from the outdate...
What fax machine? Nobody uses Fax machine anymore – do they? Well, outside of the medical, banking, legal, insurance, and real estate industries, few people have little need of faxing things ...
Security researchers working for Volexity have discovered a novel malware which uses Emojis sent via a custom Discord server that has the ability to control compromised Linux distributions. Volexity s...
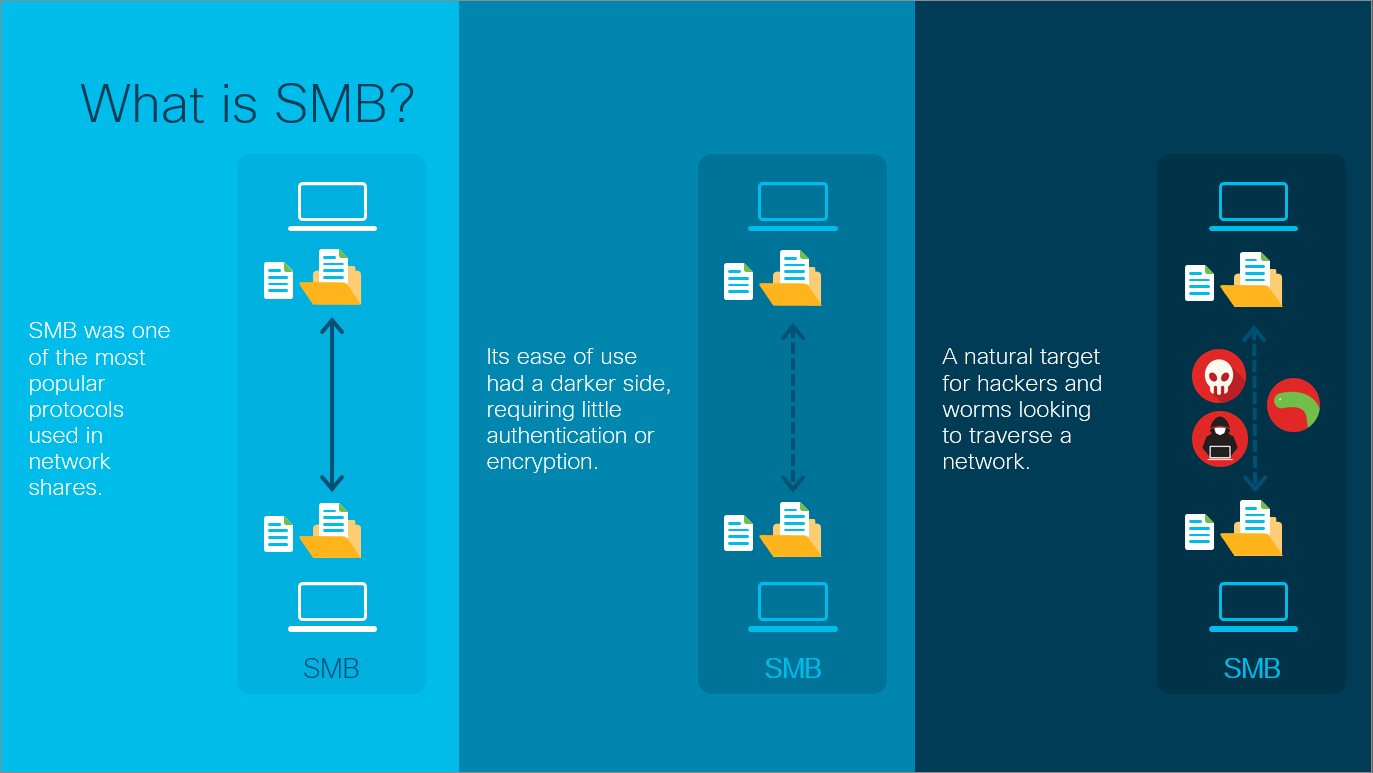
In the previous post, I covered the SMB protocol and how it has become one of the most widely used protocols in modern networks in one form or another regardless of operating system used. This post co...