New year, new beginnings and all that. This year I have set myself a challenge of writing a new blog post every day. They may be good, they may be bad, they may be interesting, they may not be, but it...
The YellowKey and GreenPlasma Zero-Days: Rethinking Windows Security and BitLocker Encryption *I know the adage is Blue & Green. but it didn’t fit the title! On the 12th of May, the cybersec...
In the ever-evolving cyber landscape, threat actors are continuously finding new ways to bypass our defences to gain access to the systems we use. Researchers at cybersecurity firm CYFIRMA have uncove...
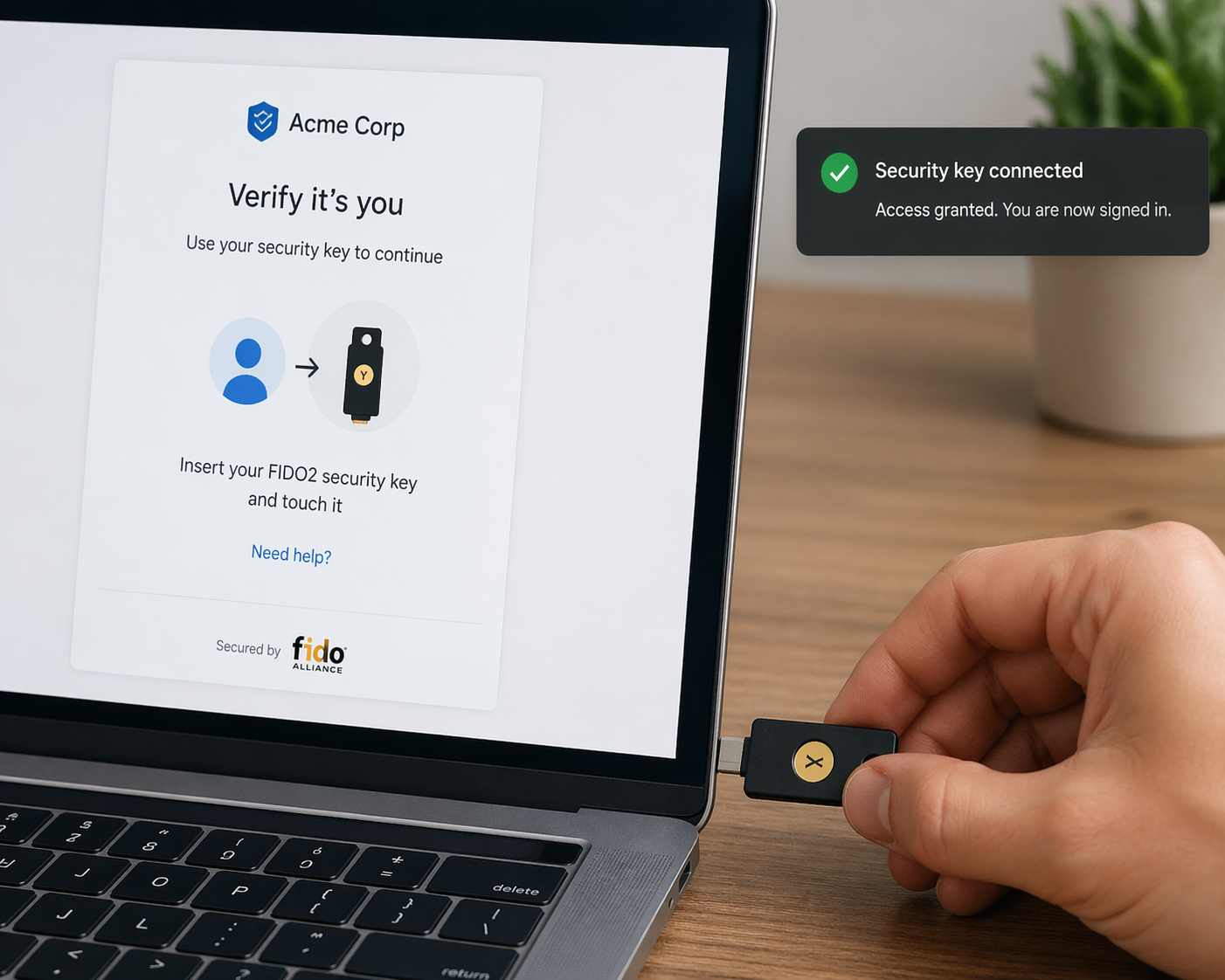
I’ve written about the use of passkeys in favour of passwords a few times over the last couple of years (see below), and this week sees a publication of a paper by the UK’s NCSC that re-en...
Microsoft have pushed out a number of updates in their April 2026 release, and one of them has been a long time coming – An update to how Windows handles RDP connectivity The main change for thi...
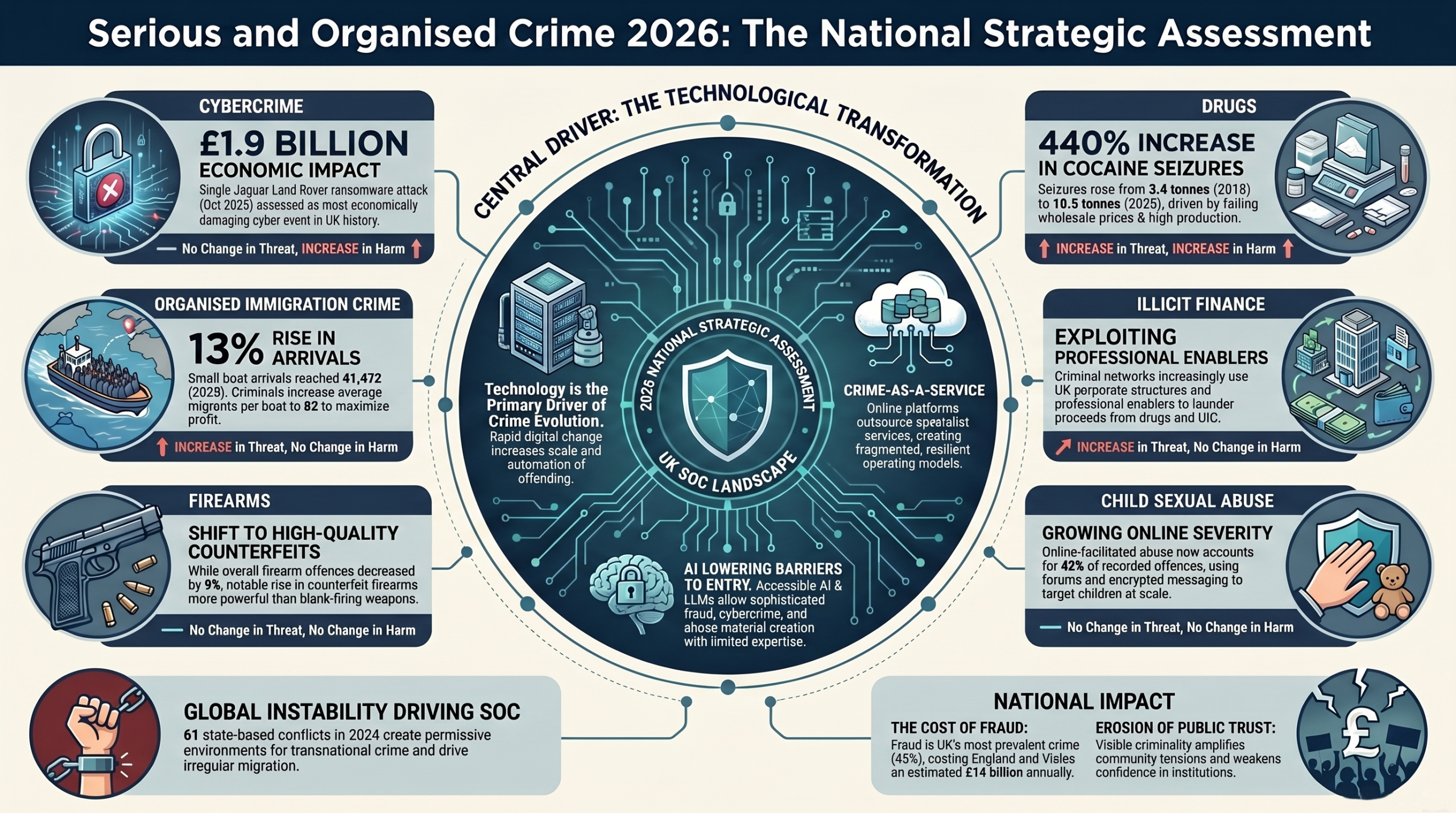
The UK’s National Crime Agency (NCA) published its 2026 National Strategic Assessment of Serious and Organised Crime (SOC) in March, and the message is unequivocal: technology is no longer just an ena...
A paper written by security researchers from Shanghai Jiao Tong University & UCLA Irvine which was revealed at the 2026 Network and Distributed System Security (NDSS) Symposium has identified the ...
For four decades, the Border Gateway Protocol (BGP) has functioned as the glue holding the internet together. It was designed to route packets between thousands of networks on the internet (A.K.A. Aut...
Security researchers at Black Lotus Labs have uncovered a sophisticated new malware called “KadNap” that has secretly hijacked over 14,000 devices worldwide to create a massive botnet. If ...
Google’s Threat Intelligence Group (GTIG) has uncovered a massive new iOS exploit kit dubbed “Coruna”. The malware targets Apple iPhone models running iOS 13.0 through to iOS 17.2.1,...
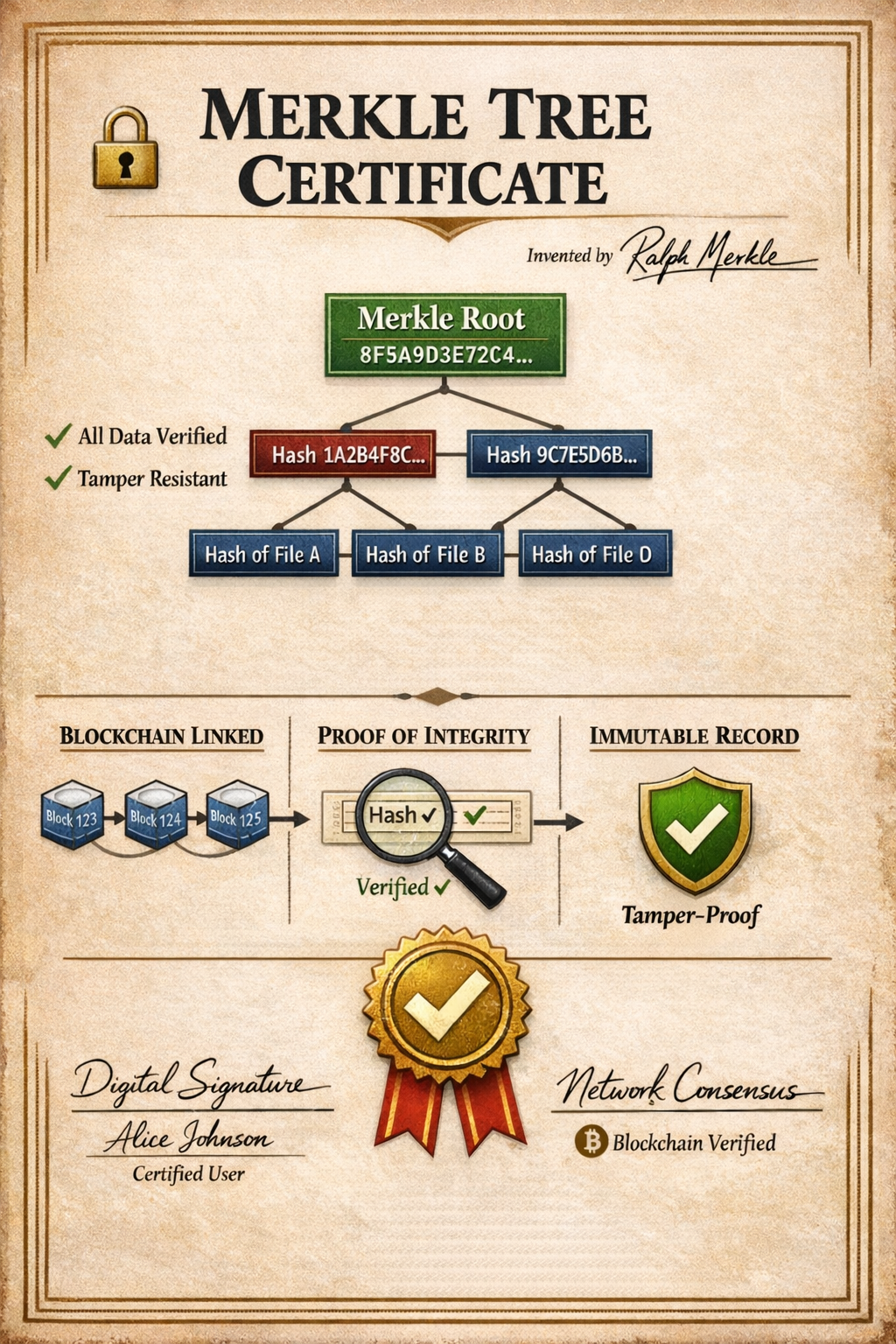
The impending reality of quantum computing poses a significant threat to the cryptographic standards that secure the Internet today. To stay ahead of this threat, the developers of Google Chrome have ...