The impending reality of quantum computing poses a significant threat to the cryptographic standards that secure the Internet today.
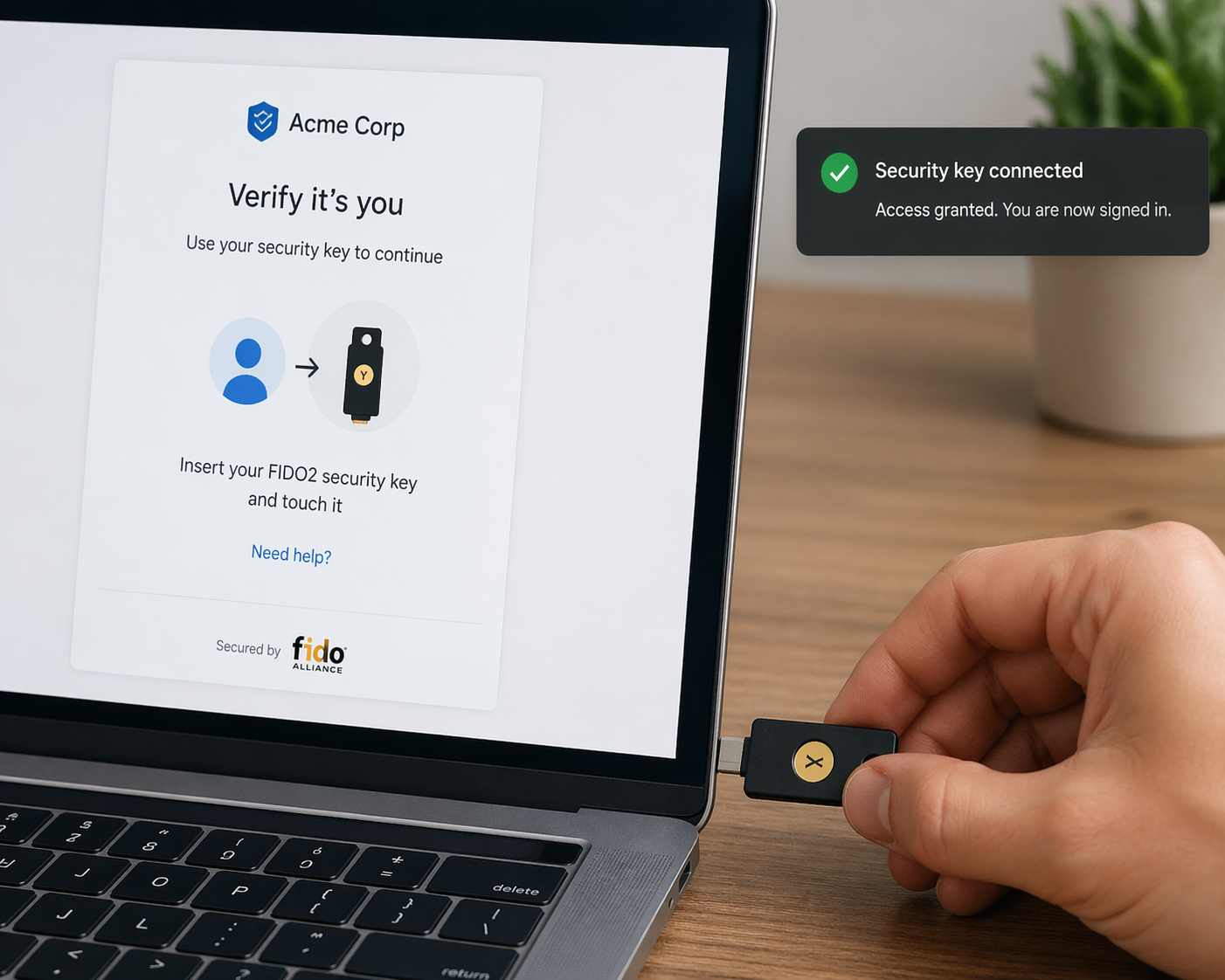
To stay ahead of this threat, the developers of Google Chrome have announced a new program designed to make HTTPS certificates secure against quantum computers. Partnering with the Internet Engineering Task Force’s (IETF) new working group – PKI, Logs, And Tree Signatures, (PLANTS), this initiative aims to tackle the performance and bandwidth issues introduced by quantum-resistant cryptography.
The Problem with Traditional Certificates
As we move to quantum-resistant cryptography, the traditional digital certificates used by websites which are based on the X.509 standard, face a major bottleneck – size.
Integrating post-quantum algorithms into traditional, serialised signature chains incurs a massive bandwidth penalty that threatens to slow down TLS connections. Because of these scalability and efficiency issues, Google has no immediate plans to add traditional X.509 certificates equipped with post-quantum cryptography to the public Chrome Root Store, however Google does plan to support “traditional” X.509 certificates with quantum-resistant algorithms for private PKIs.
So what’s the solution?
The solution is Merkle Tree Certificates (MTCs). MTCs replace heavy signature chains with compact Merkle Tree proofs.
In this innovative model, a Certification Authority (CA) signs a single “Tree Head” that can represent potentially millions of certificates. Browsers are then sent a lightweight proof of inclusion within that tree, rather than a bulky certificate chain.
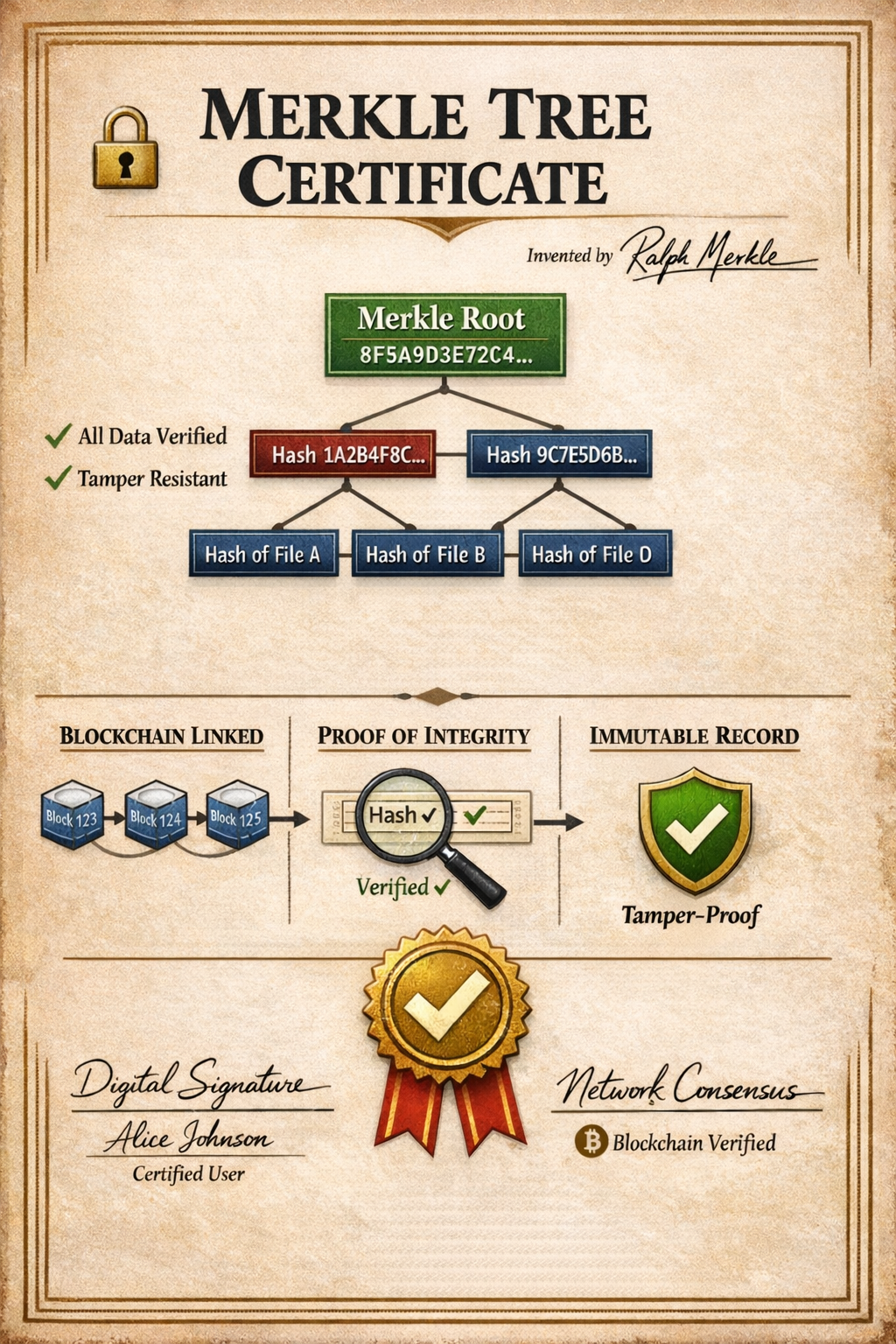
Merkle tree chains have been around since 1979 when they were invented by Ralph Merkle, they are used extensively today in modern blockchain systems.
A Merkle tree (as the name would suggest) is a tree-shaped structure where:
- Each leaf node contains a hash of some data
- Each parent node contains a hash of its two children
- The top node is called the Merkle root
Suppose you have four files:
1,2,3,4
Produce a hash of each file
Hash(1), Hash(2), Hash(3), Hash(4)
Combine pairs of hashes and hash them to produce parent hashes (P)
P1= Hash(Hash(1)+Hash(2))
P2= Hash(Hash(3)+Hash(4))
Hash these together to produce the Merkle root (Mr)
Mr = Hash(Hash(P1) + Hash (P2))
This final hash represents all four files in hash format, if one hash changes, the Merkle root changes
Why MTCs are a game-changer:
- Speed and Efficiency: MTCs decouple the security strength of the cryptographic algorithm from the amount of data being transmitted, shrinking authentication data in the TLS handshake to the absolute minimum to keep the web running as fast as possible.
- Built-in Transparency: With MTCs, it is impossible to issue a certificate without including it in a public tree. This builds the security properties of the current Certificate Transparency (CT) ecosystem in by default, without the extra overhead.
Chrome is already testing MTCs with real internet traffic and has outlined a three-phase approach to propagate this technology globally.
Phase 1: Feasibility Study (Underway) In collaboration with Cloudflare, Chrome is currently evaluating the real-world performance and security of MTC-based TLS connections. To ensure stability, every MTC connection in this phase is acting as a “fail safe” and is backed by a traditional, trusted X.509 certificate.
Phase 2: Bootstrapping (Targeting Q1 2027) Once validated, Chrome will invite established CT Log operators (specifically those with a “usable” log before February 1, 2026) to help bootstrap public MTCs. Because MTC technology shares architectural similarities with CT logs, these operators are uniquely qualified to get the MTC ecosystem off the ground quickly.
Phase 3: The New Root Store (Targeting Q3 2027) Chrome will finalize requirements to onboard CAs into a brand new trust store: the Chrome Quantum-resistant Root Store (CQRS). This Root Program will exclusively support MTCs and will operate alongside the existing Chrome Root Program for a risk-managed transition. Sites will also be able to opt-in to downgrade protections, ensuring they only use quantum-resistant certificates.
Beyond just swapping algorithms, Google views the shift to MTCs as an opportunity to modernise the foundational practices of the web.
As this rapidly evolving initiative progresses, Chrome plans to share a concrete policy framework to guide organizations in becoming Chrome-trusted MTC CAs, ensuring a secure, resilient, and post-quantum future for the web.
More information about this new approach to a quantum-proof web can be read at Cloudflare, and Google‘s own blog posts
Post 73 – 03/03/2026