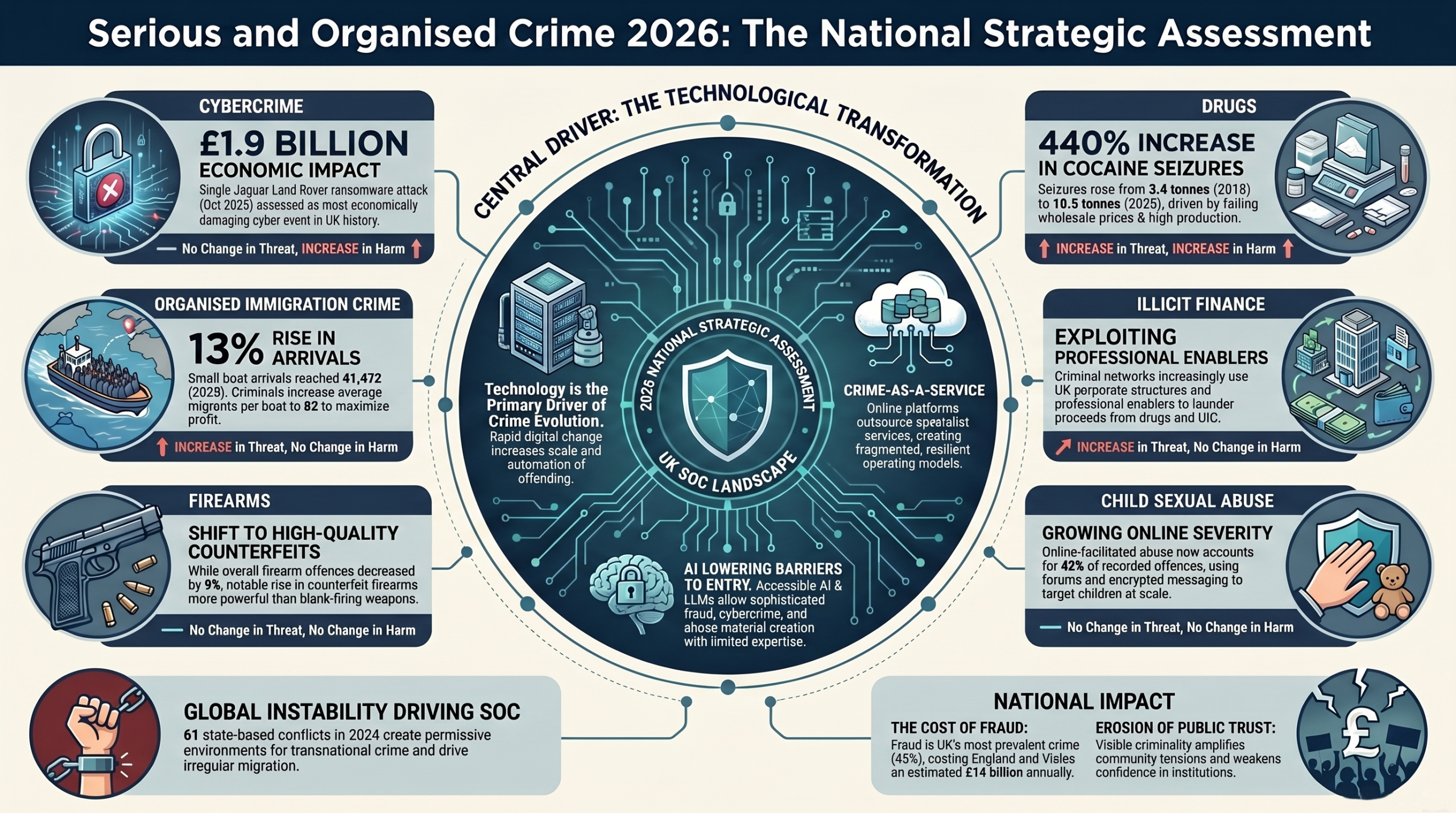
The UK’s National Crime Agency (NCA) published its 2026 National Strategic Assessment of Serious and Organised Crime (SOC) in March, and the message is unequivocal: technology is no longer just an enabler of crime; it is driving a large-scale transformation in its scale, sophistication, and resilience.
The assessment analyses the threat through five core domains:
- Within communities
- At the border
- Transnationally
- Online
- Within finance
The assessment highlights how threat actors are converging their efforts, exploiting global instability, and leveraging digital ecosystems to maximise harm.
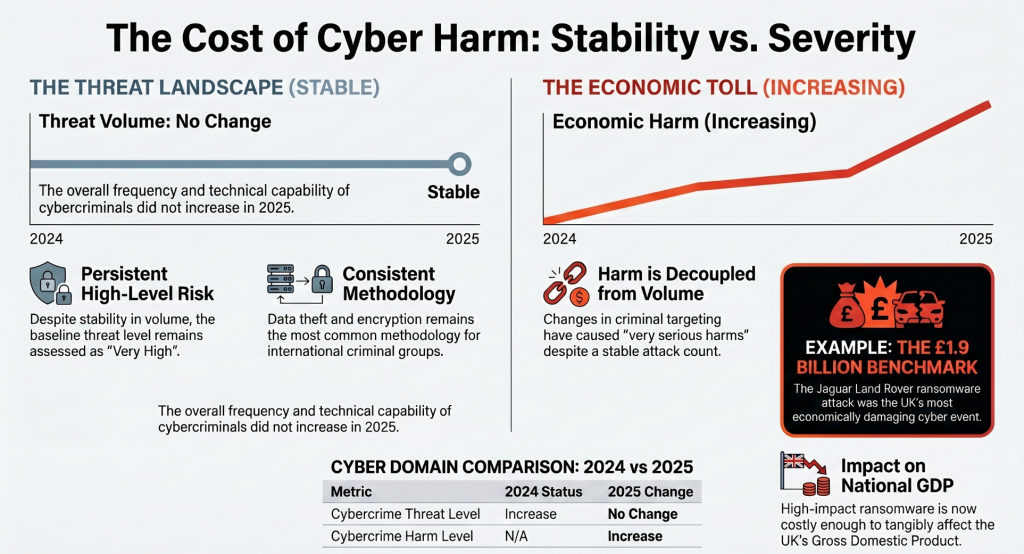
The Cybercrime Paradox: Stable Threat, Skyrocketing Harm
The overall threat volume from serious and organised cybercrime to the UK did not technically increase in 2025. However, the harm generated by these attacks escalated dramatically, driven by a small number of devastating ransomware incidents such as the attack on Jaguar Land Rover (JLR), which the Cyber Monitoring Centre classified as the most economically damaging cyber event to hit the UK to date. The estimated cost to the UK economy was a staggering £1.9 billion, a figure so substantial that it tangibly impacted the nation’s gross domestic product.
Data theft and encryption remain the core methodologies, with attacks predominantly orchestrated by financially motivated actors based overseas. Interestingly, the report notes that English-speaking cybercriminals, including those based in the UK, have gained a distinct advantage by deploying highly sophisticated social engineering techniques, leveraging their native grasp of the language and cultural nuances to access credentials. Furthermore, the persistence of obsolete technology remains a massive vulnerability; when free security updates for Windows 10 ended in October 2025, an estimated 5 million devices in the UK were left exposed to emerging threats.
AI as the Ultimate Force Multiplier
Artificial intelligence is rapidly lowering the barriers to entry for criminality, creating an environment where low-skilled offenders can operate at an unprecedented scale. The NCA assesses that AI is increasingly identifying software vulnerabilities at a rapid pace, automating elements of cyberattacks, and enabling the mass targeting of victims.
Large Language Models (LLMs) and AI-powered translation tools are actively being weaponised to eliminate language barriers, allowing non-English speaking threat actors to target UK citizens and organisations with highly plausible, tailored phishing and social engineering scripts.
Deepfake technology is also eroding trust in institutions; the NCA warns that threat actors are highly likely to introduce deepfakes into criminal trials to provide false alibis or undermine the credibility of witnesses and judges. Furthermore, the rise of AI “companion apps” has created a new vector for romance fraud and extortion, with poorly secured legitimate apps leaving user data vulnerable to scraping and exploitation.
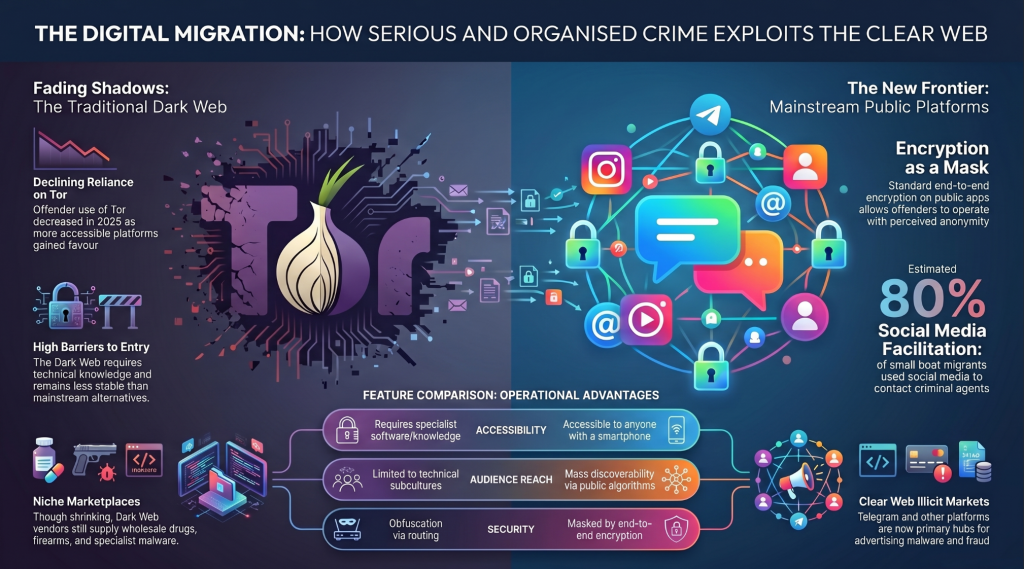
The Surface Web is the New Dark Web
One of the most startling operational shifts covered in the report is the migration of criminal activity away from the dark web. While Tor remains a hub for illicit marketplaces, its use by offenders decreased in 2025.
Instead, threat actors are migrating to clear web platforms because mainstream communication platforms now offer end-to-end encryption as a standard feature, require far less technical expertise to navigate, and are highly stable.
Fraud-enabling tools – such as ransomware strains, stolen datasets, malware, and phishing kits are increasingly being advertised and sold on platforms like Telegram. These platforms act as networking hubs where a small number of highly capable offenders can crowdsource their tradecraft, share knowledge, and offer cybercrime-as-a-service to a global criminal audience. Web 3.0 has become a cyber criminals place to do business.
Global Instability and State-Sponsored Convergence
The blending of geopolitical conflict and cybercrime is creating highly permissive environments for threat actors. The NCA highlights the explosive growth of “fraud compounds” a phenomenon that began in the conflict zones in South East Asia (like Myanmar) and is now spreading globally. For example, in 2025, a massive compound was dismantled in Ghana, where over 200 trafficked individuals were forced into modern slavery to conduct global romance fraud.
The lines between financially motivated cybercrime and state-sponsored espionage also continue to blur. Hostile states (notably Russia and Iran) are highly likely to be using cybercriminals as proxies to pursue strategic objectives against the UK. This outsourcing grants states plausible deniability while enabling them to evade sanctions, fund operations, and subvert Western authority through cyber sabotage.
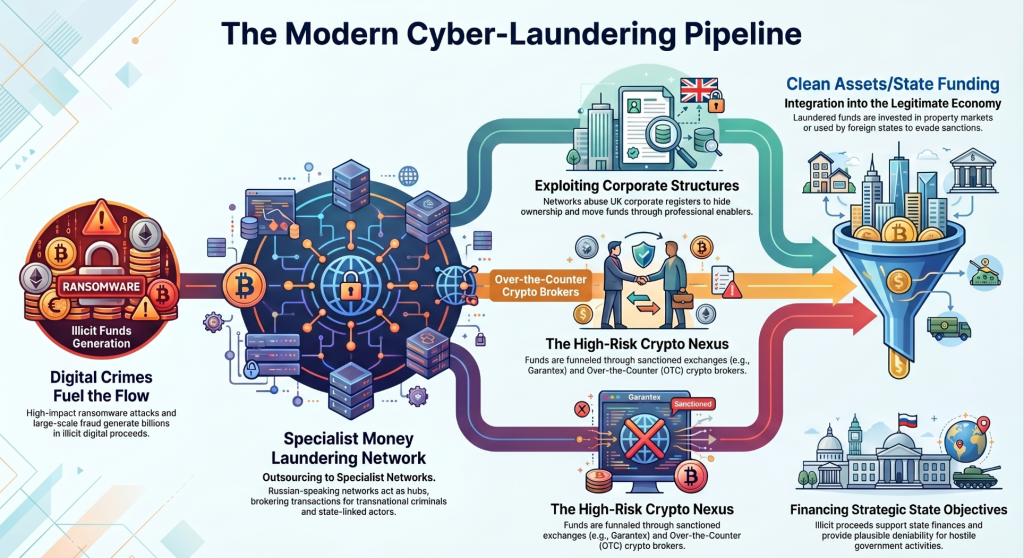
The Cyber-Finance Nexus: Outsourced Money Laundering
Organised crime groups are increasingly fragmenting their operations, preferring to outsource money laundering to specialist, highly technical networks. Russian-speaking money laundering networks have become particularly prominent, servicing a diverse clientele that ranges from traditional drug cartels to hostile state-linked entities.
These networks act as brokers, coordinating the conversion of criminal cash into cryptocurrency, often relying on sanctioned cryptocurrency exchanges like Garantex to bypass traditional Western financial systems. The NCA’s Operation DESTABILISE resulted in 129 arrests and the seizure of over £25 million in cash and crypto, exposing direct links between street-level laundering in the UK and Russian intelligence services.
Furthermore, researchers should monitor the financial markets, where cyber-enabled “pump and dump” schemes have increased. Overseas trading groups are leveraging social media disinformation and bogus financial news sites to manipulate UK share prices, a threat that will almost certainly be exacerbated by AI-generated content in the coming years.
Final thoughts
The 2026 National Strategic Assessment makes it clear that cybersecurity is no longer a niche technical discipline; it is the frontline of defence against almost all forms of serious and organised crime. As threat actors continue to diversify, automate, and hide within encrypted clear-web ecosystems, security teams and researchers must adopt an equally interconnected approach.
Post 78 – 05/04/2026