Microsoft have just released the latest Digital Defence Report, and the findings are not great. The report is one which Microsoft produces annually and this latest one covers the period from July 2022...
It’s a well known fact that cyber attacks are becoming more and more commonplace in times of conflict – that much is well-established with the Russian attacks on Ukraine. Russia and Ukrain...
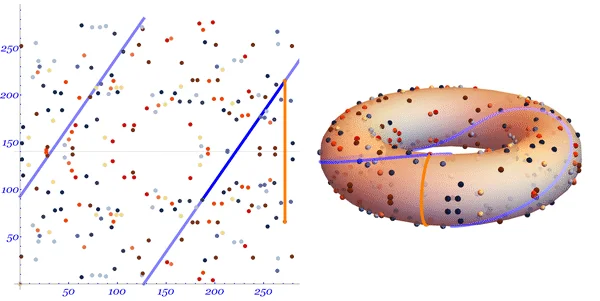
Cryptography specialist Filippo Valsorda has issued a challenge for the first person to crack the seed values for elliptic curve cryptography and recover the plain text values which were used to gener...
Twenty-Two year-old Sebastien Raoult, a French citizen from the eastern town of Epinal has submitted a guilty plea to the U.S. Attorney’s office in Washington. Raoult, who was known online as Se...
Last weekend, users of the mobile network Lyca started to experience difficulties using the network, especially when trying to log in to their user accounts to top-up their credit. Following these eve...
A number of Proof-Of-Concept (PoC) exploits have surfaced on the Internet which target a high-severity flaw in a number of Linux distributions which give attackers Root privileges if sucessful. The vu...
The International Committee of the Red Cross (ICRC) has issued a first-of-its-kind rules of engagement for civilian hackers in conflicts. The organisation released the rules this week in the wake of u...
Researchers at securityaffairs have released an fascinating insight in to the global infrastructure used by LockBit during their ransomware attacks. The blog post : “LIGHTING THE EXFILTRATION IN...
Security researchers at Zscaler have discovered a new malware-as-a-service (MaaS) named ‘BunnyLoader’ being advertised on multiple dark web forums as a file-less loader that can perform mu...
North Korean hacking group – Lasarus are currently running a targeted campaign against people in specific industry sectors via an elaborate social engineering campaign dubbed Operation DreamJob....