This week saw a combined effort from law enforcement and judicial authorities from eleven countries deliver a major blow to one of the most dangerous ransomware operations of recent years. The Ragnar_...
Google’s Threat Analysis Group (TAG) have released a statement this week showing that multiple government-backed threat actors are actively exploiting a vulnerability within the WinRAR archiving...
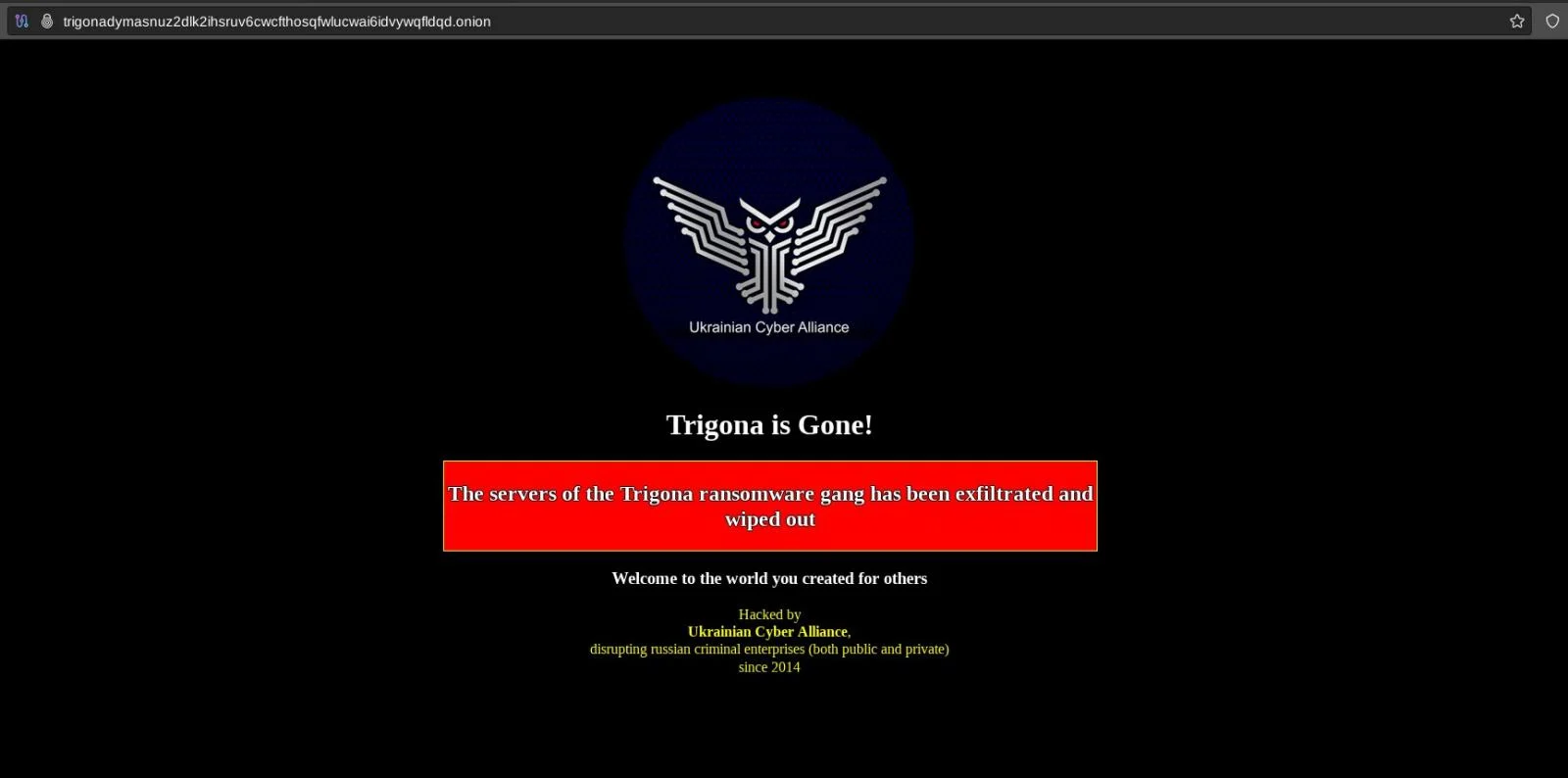
A post uploaded yesterday by @vx_herm1t on X shows the current home page of Russian ransomware gang Trigona and that it has appears to have been completely wiped out by the Ukrainian Cyber Alliance. W...
In the last post, I discussed the properties of cryptographic keys, and the different types of keys used in cryptography. One of the examples I gave was the one of key exchange, and that in modern sys...
So far in this short guide to encryption, we have looked at some of the terms associated with an encryption system, and some of the desirable qualities such a system should have. We have explained the...
One of the desirable properties of an encryption system is that of high variance, or entropy. The larger the number of possible values in a key, the harder it is to work out what the key could be. In ...
In the previous post, I identified a few common terms used in encryption, and then identified some early examples of ancient encryption . In those early methods of securing data, we see three more fun...
We all know encryption is the no.1 tool used to keep data private – we hear it mentioned everywhere, but to many it’s just some magical thing involving hard maths that just works right? We...
SolarWinds, MoveIT, NotPetya, CCleaner, Equifax, Target. All the above names have one thing in common – at some point, all of these have been involved in large supply chain attacks which have af...
On Tuesday (10th) Google announced that Passkeys were now the default sign-in option across all personal Google accounts across all services and devices. This step will make using Google products a mu...