Those of you who followed my 365 days of blogs last year will remember I posted a few times of the story concerning the stolen data sharing forum Breached.vc, the arrest of the site admin, and the sub...
It is impossible to not have noticed the flurry of activity surrounding the new generation of AI technologies in the last 12 months. Whilst AI has been around in one form or another for decades, the l...
A hacker who goes by the name The McFlurry bandit has compromised McDonalds twice in recent weeks. The first attack came on the 10th January when the attacker posted that they had compromised the McDo...
Security researchers at SentinelOne have released information regarding a newly discovered malware which is being actively used to target cloud and payment services. The Python-generated malware is ca...
The National Cyber Security Centre yesterday (11th Jan 2024) launched new guidance for small businesses to help them safely use online services such as cloud computing, web hosting, online accounting,...
When most people think about a cyber attack, they think of things like a phishing attack that allows a threat actor to trick an employee into giving up data, or a Denial of Service attack that stops l...
A 72-page report produced by the Joint Committee on the National Security Strategy has criticised the UK’s ability to cope with ransomware attacks and has revealed that “large swathes of U...
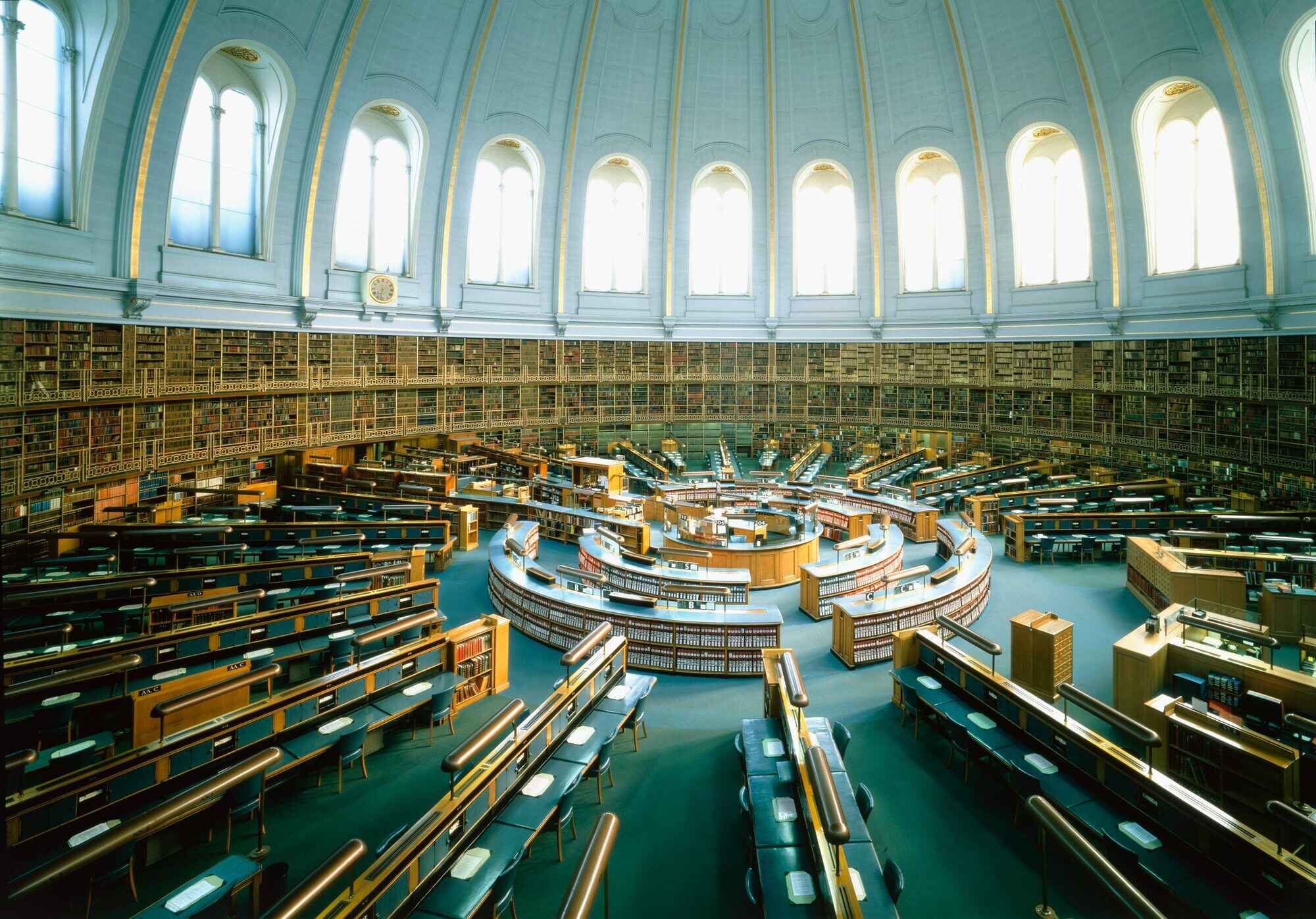
Those of you who followed my 365 days of blogs last year will possibly remember that I uploaded a couple of posts about the ransomware attack on the British Library back in August and November. The Li...
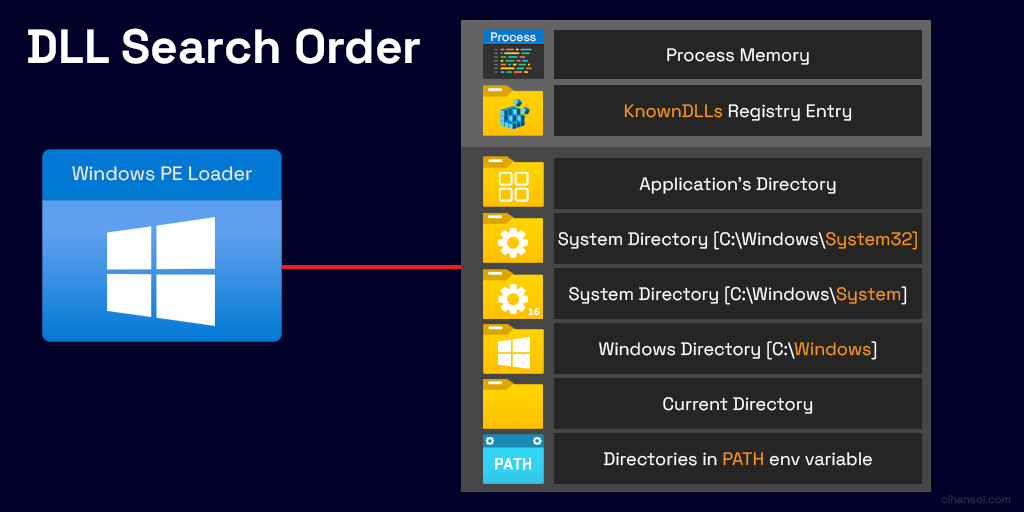
Security researchers at securityjoes.com have published a paper detailing a new mechanism that allows threat actors to bypass Windows 10 & Windows 11 security controls by leveraging DLLs commonly ...
DNS, or the Domain Name System, is the system that translates human-readable website names (such as cybertrainer.uk) into the numerical IP addresses that computers on the Internet use to communicate w...