Google’s Threat Intelligence Group (GTIG) has uncovered a massive new iOS exploit kit dubbed “Coruna”. The malware targets Apple iPhone models running iOS 13.0 through to iOS 17.2.1,...
Most people who use a guest Wi-Fi network, such as the one in a hotel, or the local coffee shop assume that their device and communications are secure, and for a number of years this has been the case...
Watch any Hollywood movie that contains a scene where a nerd is tasked with hacking some IT system and its a flurry of fingers across a keyboard and then a few seconds later, the immortal shout of ...
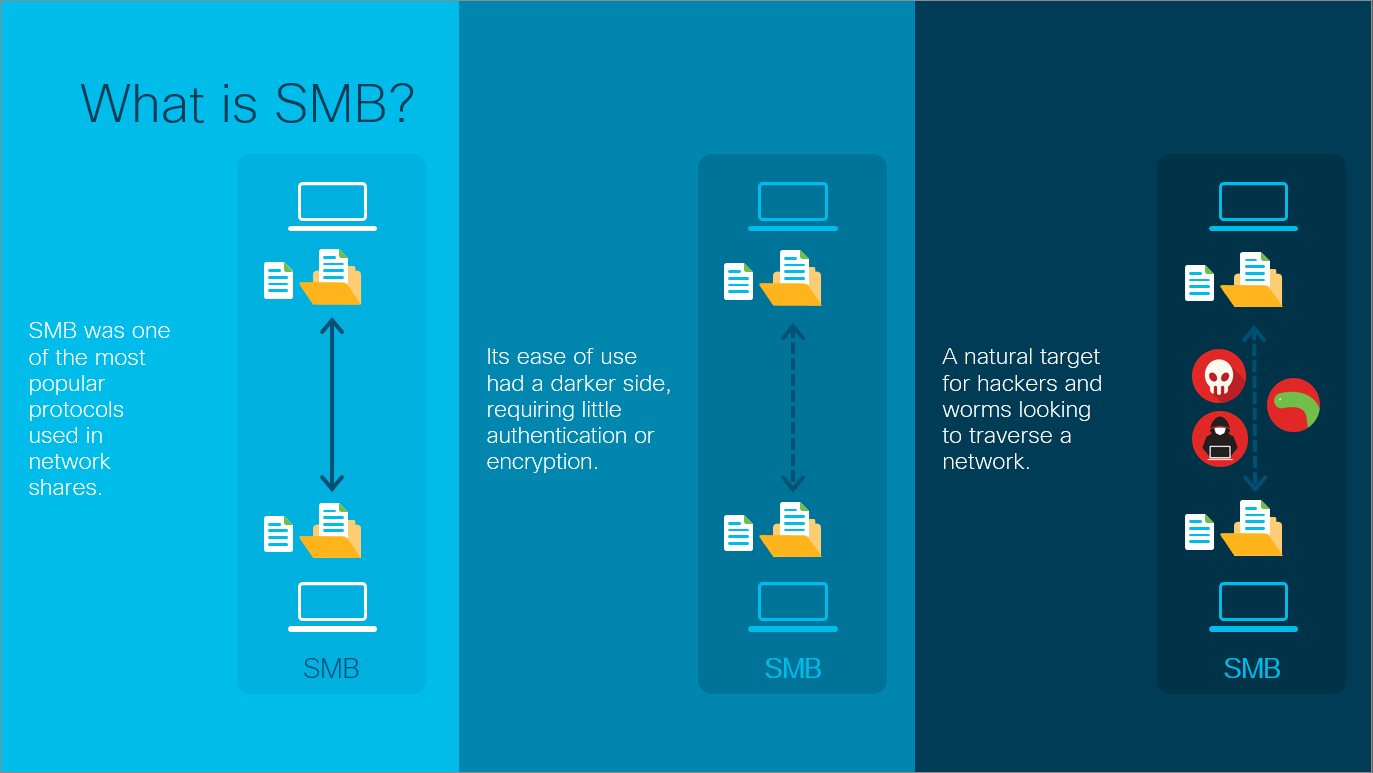
In the previous post, I covered the SMB protocol and how it has become one of the most widely used protocols in modern networks in one form or another regardless of operating system used. This post co...
Yesterday (12th February), saw the release of a new set of guidance documents by the National Cyber Security Centre (NCSC). The guidance concerns vulnerability management, and is aimed at a wide range...
Security researchers at SentinelOne have released information regarding a newly discovered malware which is being actively used to target cloud and payment services. The Python-generated malware is ca...