Gopherware (Gopher malware) is the term given to malware written in the Go (Golang) programming language. As a threat, gopherware has seen a massive surge in adoption by threat actors since early 2019...
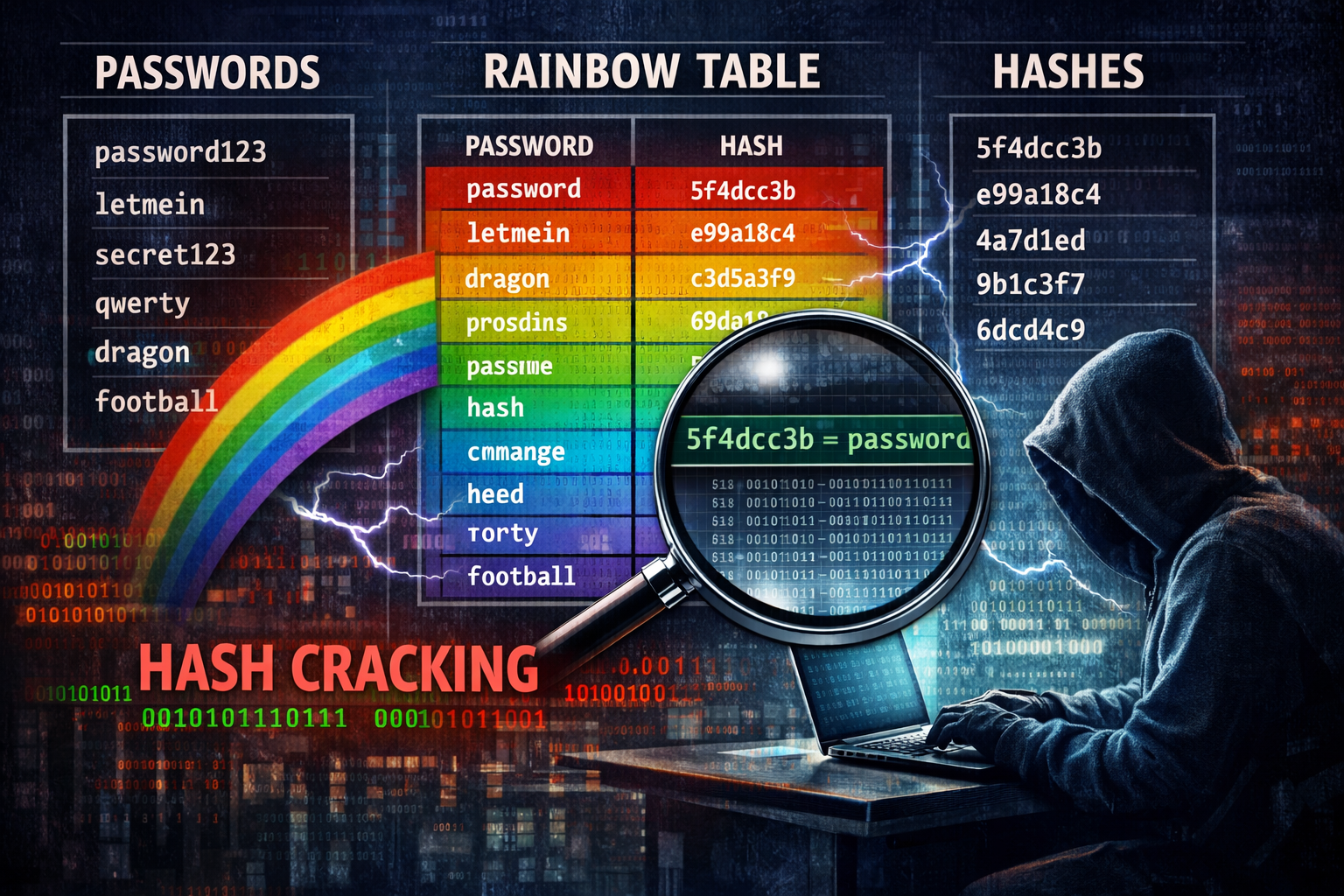
Mandiant (the Google-owned Cyber Security research company) has released a comprehensive dataset of Net-NTLMv1 rainbow tables in an attempt to force organisations to migrate away from the outdate...
Last December, security researchers at Koi Security revealed their initial findings into a novel browser exploit they have called GhostPoster In short, this exploit utilises steganography to hide mali...
A couple of vulnerabilities were added to the CVE database last year that could have devastating effects on mobile phone users who listen to music via Bluetooth headphones The CVEs in question are: As...
What fax machine? Nobody uses Fax machine anymore – do they? Well, outside of the medical, banking, legal, insurance, and real estate industries, few people have little need of faxing things ...
A new side-channel attack has been discovered that affects Android devices and could allow a threat actor to steal sensitive data from victim devices without them knowing. Called pixnapping, the attac...
A cyber security professional needs to understand many things in order to have some level of success in defending the systems in their care – A small sample of those things include: Within those...
Active Cyber Defence (ACD) is the title given to a range of technologies and processes set up by the NCSC to help make the UK the safest place to live and do business online. Active Cyber Defence (ACD...
This week, the National Crime Agency (NCA) announced the successful takedown of a Crimeware As A Service (CaaS) platform that offered the ability to spoof telephone numbers which was used by criminals...
Security researchers working for Volexity have discovered a novel malware which uses Emojis sent via a custom Discord server that has the ability to control compromised Linux distributions. Volexity s...