Gopherware (Gopher malware) is the term given to malware written in the Go (Golang) programming language. As a threat, gopherware has seen a massive surge in adoption by threat actors since early 2019...
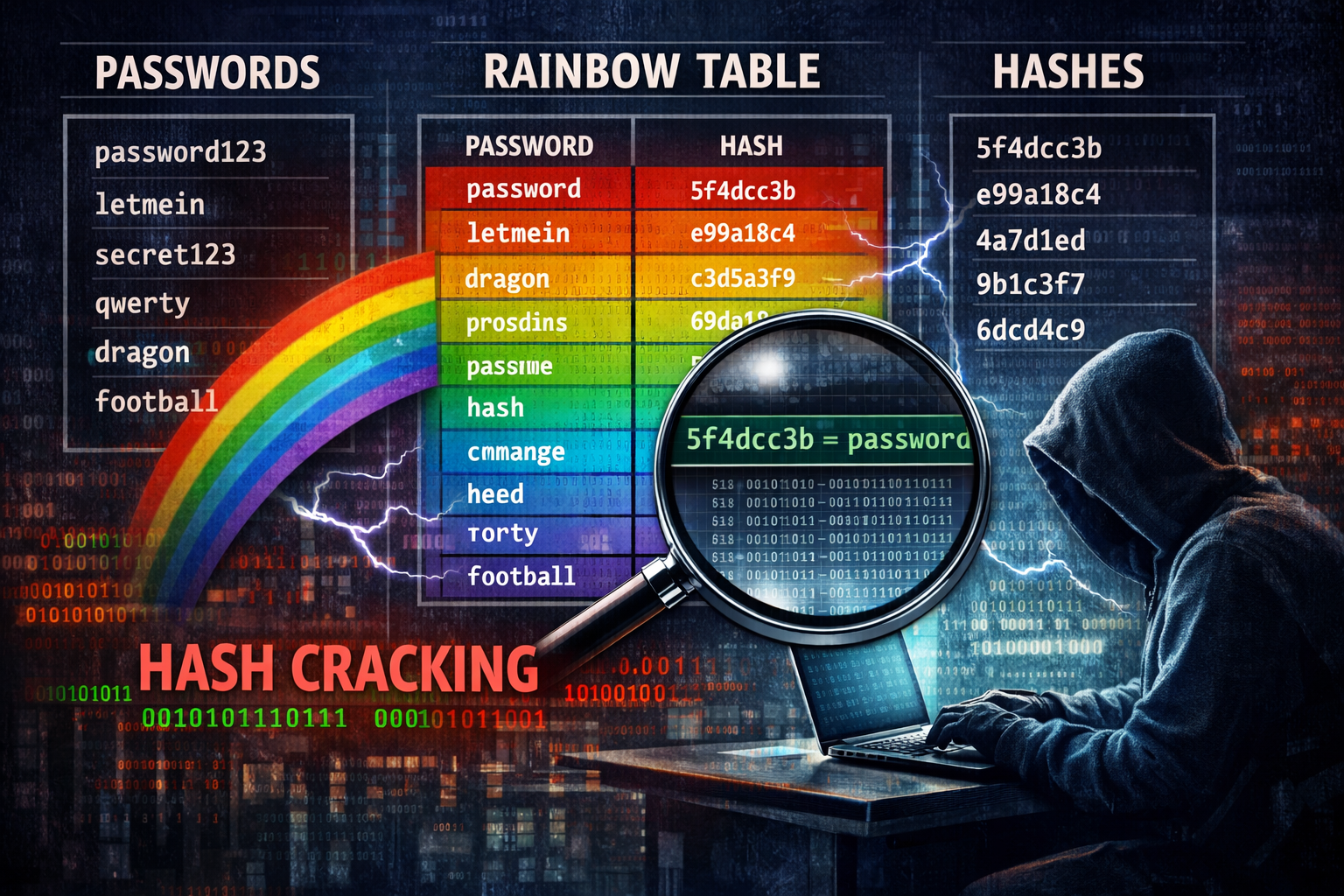
Mandiant (the Google-owned Cyber Security research company) has released a comprehensive dataset of Net-NTLMv1 rainbow tables in an attempt to force organisations to migrate away from the outdate...
Last December, security researchers at Koi Security revealed their initial findings into a novel browser exploit they have called GhostPoster In short, this exploit utilises steganography to hide mali...
A couple of vulnerabilities were added to the CVE database last year that could have devastating effects on mobile phone users who listen to music via Bluetooth headphones The CVEs in question are: As...
What fax machine? Nobody uses Fax machine anymore – do they? Well, outside of the medical, banking, legal, insurance, and real estate industries, few people have little need of faxing things ...
A new side-channel attack has been discovered that affects Android devices and could allow a threat actor to steal sensitive data from victim devices without them knowing. Called pixnapping, the attac...
Unless you’ve been living under a rock this last couple of months, you can’t fail to have heard about the cyber-attack that hit Jaguar-Landrover (JLR) in the last week of August. In this p...
I’ve written about this sort of thing before, but I keep seeing many “closing down” sob-stories on Facebook, so though it time to write another post showing how to tell if a site rea...
Windows Administrator accounts have the highest level of access and control over the computer system, and are used to manage user accounts, install software, change system settings, and access all fil...
Almost a year to the day (30 & 31st June 2024) I posted about Operation Endgame – the operation, spearheaded by the National Crime Agency (NCA) to takedown several high-profile botnets, incl...