365 days of blogs
New year, new beginnings and all that. This year I have set myself a challenge…
DualStrike – Real-time attacks against commodity keyboards
A paper written by security researchers from Shanghai Jiao Tong University & UCLA Irvine which…
Is it time to replace BGP? SCION thinks so
For four decades, the Border Gateway Protocol (BGP) has functioned as the glue holding the…
KadNap Botnet compromises 14K+ devices worldwide
Security researchers at Black Lotus Labs have uncovered a sophisticated new malware called "KadNap" that…
Coruna: A very powerful iOS exploit kit
Google's Threat Intelligence Group (GTIG) has uncovered a massive new iOS exploit kit dubbed "Coruna".…
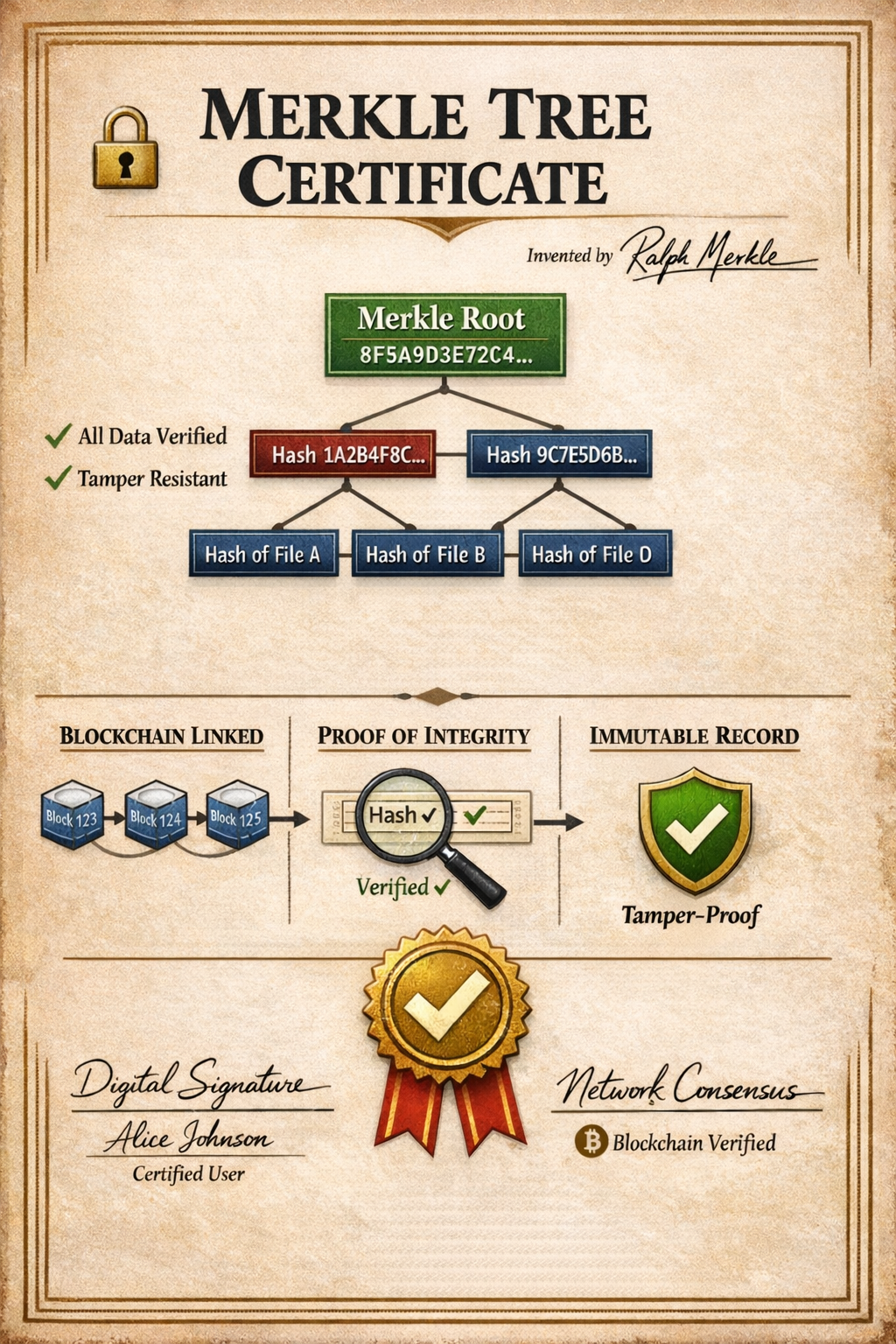
Securing the Post-Quantum Web: Chrome’s shift to Merkle Tree Certificates
The impending reality of quantum computing poses a significant threat to the cryptographic standards that…
USB – not all as it may seem
We all have one. It might be a box, an old carrier bag, or even…
AirSnitch – a MiTM attack for Wi-Fi
Most people who use a guest Wi-Fi network, such as the one in a hotel,…
SMS scammers sentenced
A British Transport Police (BTP) investigation has resulted in four men being sentenced to jail…
What is gopherware?
Gopherware (Gopher malware) is the term given to malware written in the Go (Golang) programming…
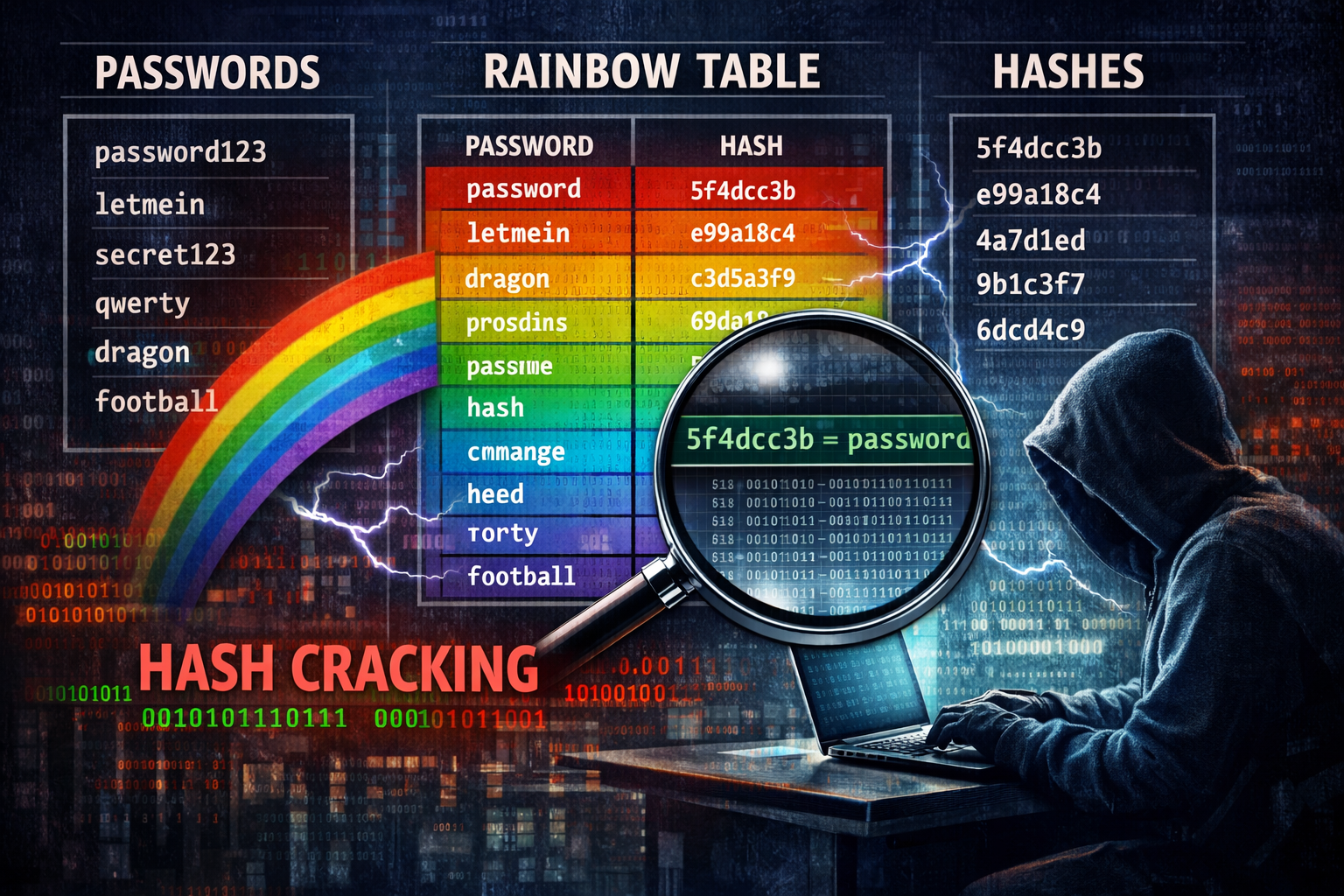
Net-NTLMv1 full rainbow tables released
Mandiant (the Google-owned Cyber Security research company) has released a comprehensive dataset of Net-NTLMv1 rainbow tables…