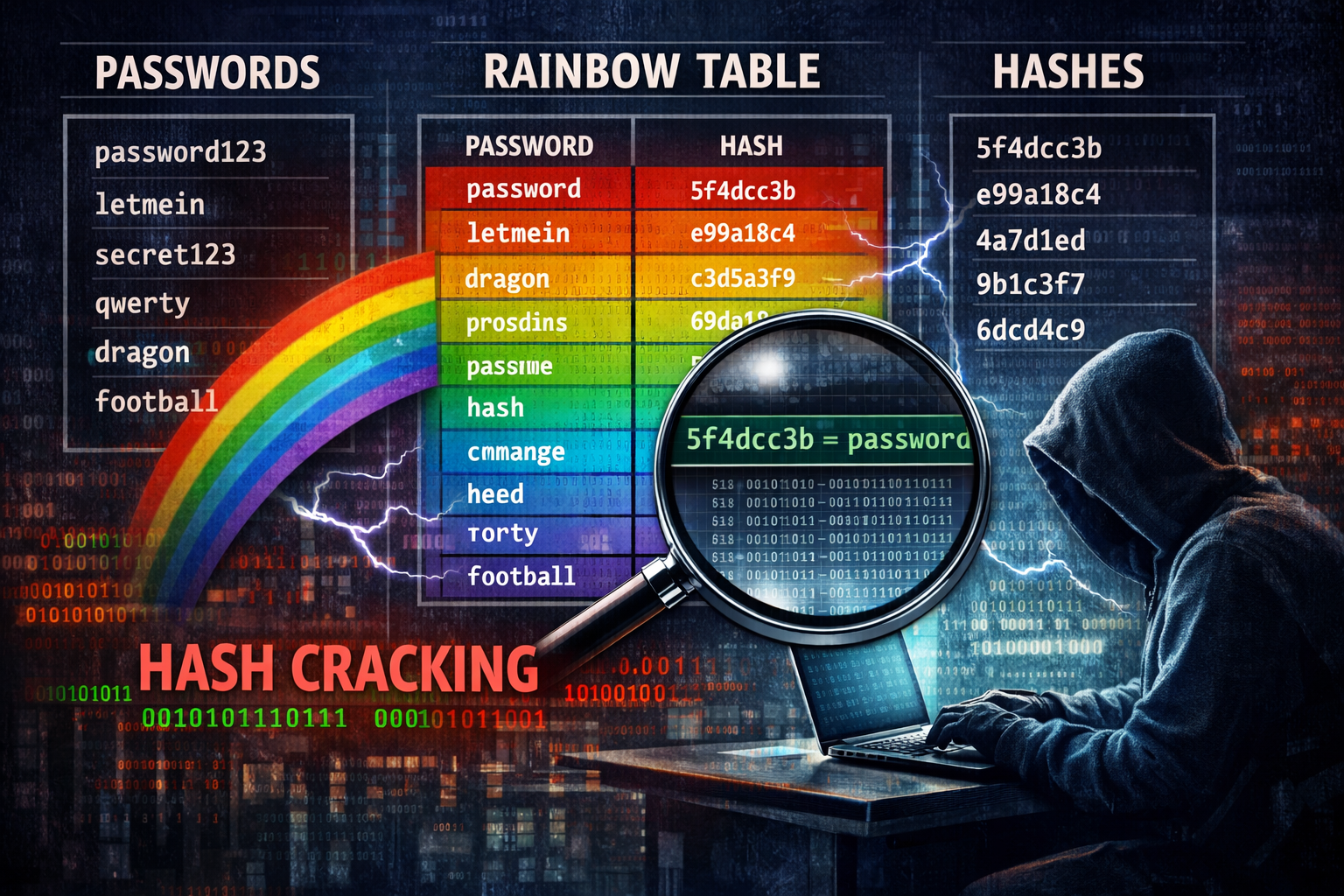
Mandiant (the Google-owned Cyber Security research company) has released a comprehensive dataset of Net-NTLMv1 rainbow tables in an attempt to force organisations to migrate away from the outdate...
Last December, security researchers at Koi Security revealed their initial findings into a novel browser exploit they have called GhostPoster In short, this exploit utilises steganography to hide mali...
A couple of vulnerabilities were added to the CVE database last year that could have devastating effects on mobile phone users who listen to music via Bluetooth headphones The CVEs in question are: As...