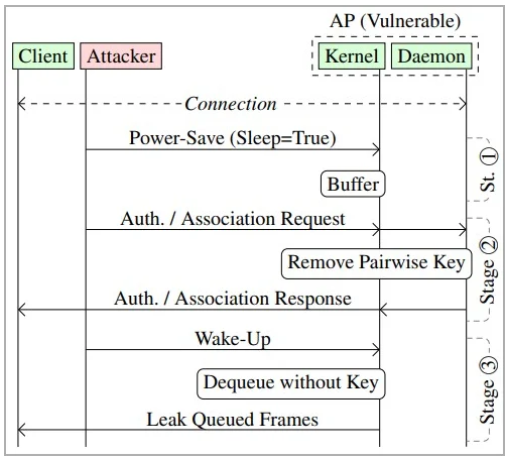
Cybersecurity researchers have discovered a vulnerability in the design of the IEEE802.11 standard – This is the standard from which Wi-Fi is based. In a paper released on Monday, the researcher...
Continuing the mini-series of posts about online security, In this installment, I’ll discuss the use of HTMLv5 for tracking purposes. As always, before I explain how you can be tracked with this...
In my last post, I talked about the use of cookies by companies when they want to track our online browsing activities. Well, cookies are just one of a number of technologies used by companies to get ...
Reducing the number of tracking technologies employed by websites is one thing I’m quite passionate about. For me, the web has become too much of a commercial space with more and more people and...
Staying anonymous online is becoming a difficult thing to achieve, but to be honest, for the majority of people, it’s not really something we should be too worried about. There are some things h...
What’s on your network? Whilst I understand that not everyone is a computer geek, or has the time to manage their home network properly, I firmly believe that everyone should have a good grasp o...
In this post, I’ll take a look at how you can check to see what issues might be present in your IT setup. Nessus Nessus is a professional vulnerability scanner made by a company called Tenable w...
In this installment of my mini-series on protecting your online activity, I’m going to discuss VPNs. What is a VPN? A VPN (Virtual Private Network) is a technology that allows you to create a se...
In this 2nd installment of my mini-series about staying safe in an ever-increasing online world, I’m going to take a look at antivirus & anti-malware solutions. Anti-malware vs Antivirus The...
So far in my 365 days of blogs, the biggest majority of my posts have been about the threats that face us when living in a digital world. So I thought it time to focus a bit more on the defensive side...