Security researchers at Black Lotus Labs have uncovered a sophisticated new malware called “KadNap” that has secretly hijacked over 14,000 devices worldwide to create a massive botnet.
If you have a standard home or small office router, particularly an ASUS model, your device might unknowingly be part of this global botnet.
What is the KadNap Botnet?
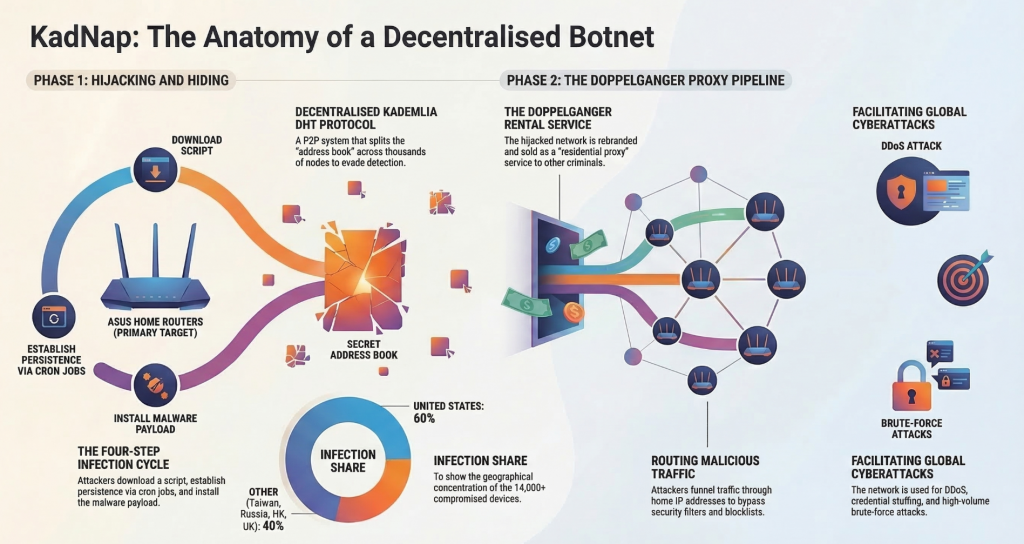
KadNap is a botnet malware that has been steadily infecting edge networking devices since August 2025. While the infections span the globe -affecting countries like Taiwan, Russia, Brazil, and the UK – the United States has been hit the hardest, with devices there accounting for over 60% of all known victims.
What makes KadNap so dangerous is its brilliant ability to hide in plain sight. Traditional botnets often rely on a central command (C2) server, which law enforcement teams can track down and shut off. KadNap, however, uses a decentralized peer-to-peer system designed to evade network detection.
It does this using a custom version of the Kademlia Distributed Hash Table (DHT) protocol.
Kademlia was designed in 2002 specifically for decentralized peer-to-peer networks such as BitTorrent, etc.
Because of this design, the malware’s communications simply blend into the normal buzz of everyday internet traffic, looking like background noise to those who might be watching for suspicious activity.
This DHT acts like a secret address book of C2 servers that makes it almost impossible for law enforcement to locate an takedown.
How Does a Router Get suborned into the botnet?
The infection process happens in a few stealthy steps:
- The Breach: A malicious script (named
aic.sh) is downloaded onto the deivce - Persistence: The script sets up a cron job that runs every 55 minutes, ensuring the malware can survive and reinstall even if the router is rebooted.
- The Payload: The main malware, an ELF binary simply named kad, is installed.
- Awaiting Orders: The router determines its external IP address, checks the current time by reaching out to various network time servers, and officially joins the botnet to wait for commands from the decentralized C2 network.
For the average victim, this whole process is invisible. The only clue you might notice is that your internet speeds occasionally feel a bit sluggish.
The Business of Cybercrime
The threat actors behind KadNap have suborned these 14,000+ hijacked devices into a proxy network which they then rent out to other criminals. The proxy service, called Doppelganger (a rebrand of an older service called Faceless), sells access to these infected devices as “resident proxies”.
Those who rent Doppelganger route their malicious traffic through your home network, effectively using your IP address as a disguise, thus giving them complete anonymity to launch distributed-denial-of-service (DDoS) attacks, brute-force campaigns, and credential stuffing attacks.
Tracing the origins of these attacks is very difficult – If law enforcement ever investigates the source of these digital attacks, the digital trail will lead right back to your front door, rather than the actual attackers.
How to Protect Yourself
There are some simple ways to ensure your devices are not targeted to join this botnet:
- Update Your Firmware: Always keep your router’s software updated to patch known vulnerabilities.
- Reboot Occasionally: Simply restarting your router every once in a while is a healthy habit.
- Change the Admin Password: Never leave your router’s default login credentials as something like “admin” and “password”.
- Restrict External Access: Check your settings to ensure your router’s administrative page isn’t accessible from the wider internet.
- Replace Old Gear: If your router is so old that the manufacturer no longer sends out security updates, it is time to buy a new one.
Take a few minutes today to log into your router and check your settings—it’s the best defense against your home network joining the dark web.
Post 75 – 15/03/2026