The FBI, working with multiple other law enforcement agencies have have seized and closed down a website which acted as a place for individuals to buy and sell data that would let them impersonate leg...
SIM swapping is a process whereby scammers convince mobile phone operators that they are you and that you want to move your number to a new device. Also known as a port-out scam, SIM splitti...
Ever keen to earn a quid buck from a situation, cyber criminals are now starting to use the spectre of ransomware attacks in an attempt to extort monies with fake ransom requests. Midnight cowboys The...
A new malware strain is targeting Android devices, and is capable of complete account takeover. Branded Nexus, the malware is a banking app trojan and has been available to threat actors since the mid...
A few days after Russia’s invasion of Ukraine (24/02/22), thousands of secret files were leaked to the German newspaper Süddeutsche Zeitung. The files were form a Russian company called NTC...
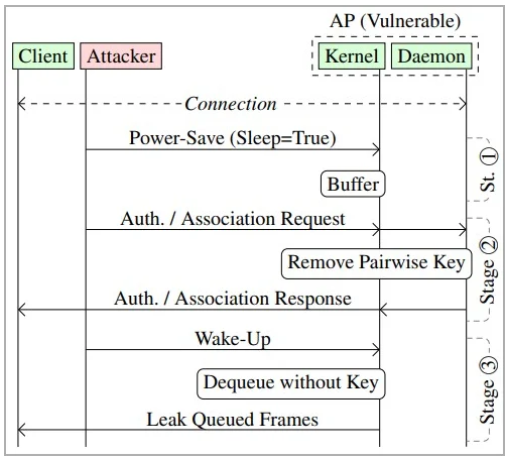
Cybersecurity researchers have discovered a vulnerability in the design of the IEEE802.11 standard – This is the standard from which Wi-Fi is based. In a paper released on Monday, the researcher...
Continuing the mini-series of posts about online security, In this installment, I’ll discuss the use of HTMLv5 for tracking purposes. As always, before I explain how you can be tracked with this...
In my last post, I talked about the use of cookies by companies when they want to track our online browsing activities. Well, cookies are just one of a number of technologies used by companies to get ...
Reducing the number of tracking technologies employed by websites is one thing I’m quite passionate about. For me, the web has become too much of a commercial space with more and more people and...
Staying anonymous online is becoming a difficult thing to achieve, but to be honest, for the majority of people, it’s not really something we should be too worried about. There are some things h...