DualStrike – Real-time attacks against commodity keyboards
A paper written by security researchers from Shanghai Jiao Tong University & UCLA Irvine which was revealed at the 2026 Network and Distributed System Security (NDSS) Symposium has identified the potential for real-time, and non-invasive attacks against popular commodity keyboards.
The attacks enable a malicious actor the ability to capture all keystrokes typed on the keyboard as well as the ability to inject of keystrokes / commands to the PC as if directly typed at the keyboard.
These attacks target the increasingly-popular hall-effect keyboards which use magnetic-field technology for smooth, precise keystrokes with ultra-fast response times, and the added benefit of being extremely durable.
Named after physicist Edwin Hall – the hall-effect is the production of a potential difference across an electrical conductor, that is transverse to an electric current in the conductor and to an applied magnetic field perpendicular to the current.
Keyboards that use hall-effect switches operate by way of a small magnet positioned under each key, so that when pressed, the magnetic field generated is altered slightly. This variation in the magnetic field is detected by a hall-sensor which, in-turn generates a small voltage representing the key press.

One of the main reasons why these types of keyboards are popular with PC gamers is that the distance between the switch and the sensor can be adjustable, giving rapid response rates than those offered by the traditional mechanical keyboard. Due to the nature of the keys, they are also silent in their operation,, which is also a sought-after feature of late-night PC users.
Eavesdropping
The researchers used a commonly-available magnetometer to measure the magnetic field strength of a hall-effect keyboard through the thickness of a typical office desk, and managed a almost 100% accuracy rate for detecting keystrokes.
The researchers also used a lightweight MLP (A form of Artificial Neural Network) to analyse the data from the magnetometer with a sampling rate of 250 Hz which is rapid enough to state that the system can offer near real-time eavesdropping of keystrokes.
Keystroke injection
To achieve controllable magnetic signal spoofing, the researchers selected electromagnets as the attack vector. In their tests, the researchers found that suction electromagnets offered a better performance due to the fact that they have an outer shield that better directs the magnetic field

A layer of magnets were placed under a hall-effect keyboard and this allowed the researchers to emit magnetic pulses to the keys, fooling them into thinking the keys had been pressed – thus achieving keystroke injection.
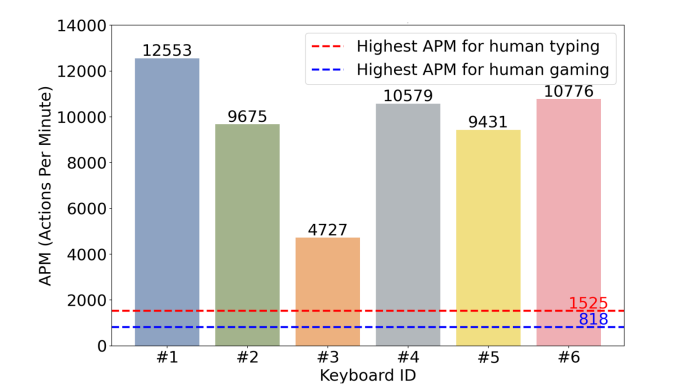
In their tests, all keyboards used achieved an injection rate of over 4,000 APM (Actions Per Minute), with one keyboard achieving 12,553 APM. considering that the highest ever recorded APM for a human typist is 1,525 APM, this is a very rapid capability of attack.
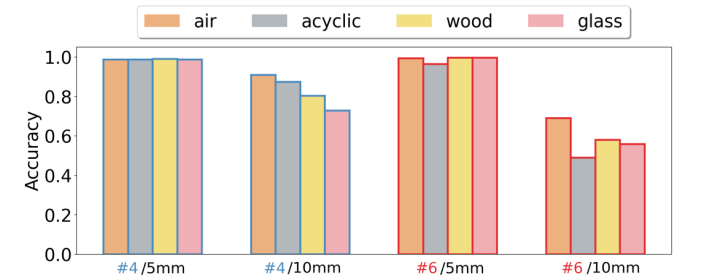
The researchers used this attack method through varying materials such as acrylic, wood, and glass at thicknesses varying between 5mm and 10mm achieving a near 100% success of injection at 5mm thickness
The researchers also accounted for the victims keyboard to be moved between attacks and built in a calibration capability into DualStrike that detected the rotation angle of the keyboard and adjusted the attack capability to suit.
By combining the calibration capibility, keystroke eavesdropping, and then keystroke injection, the researchers completed an end-to-end attack against a system by detecting the keyboard rotation, identifying the SUDO command, and subsequent password, they then repeated the SUDO and password combination to inject a series of commands to delete key files, and reformat the victim file system.
Countermeasures
Existing countermeasures against external magnetic interference are widely adopted in devices such as computers and smartphones, so the researchers tested DualStrike against keyboards using the two main types of protective measures (steel and permalloy).
The researchers used two commonly used thicknesses of 02. and 0.5 mm and found that the steel option offered minimal impact against the attacks and only slight impact was seen with the permalloy solution.
However, when the shielding was applied to individual keys, the protection worked flawlessly
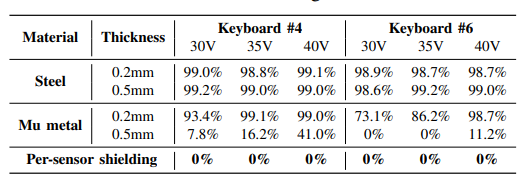
As as result, the researchers recommended a per-sensor shielding approach where a 1.5mm thick 5mm x 5mm permalloy patch is fitted beneath each hall-effect key. This method effectively blocks magnetic spoofing from below and attenuates external sensors’ ability to detect internal keystroke fields, defending against both eavesdropping and injection.