Is it time to replace BGP? SCION thinks so
For four decades, the Border Gateway Protocol (BGP) has functioned as the glue holding the internet together. It was designed to route packets between thousands of networks on the internet (A.K.A. Autonomous Systems or ASes) quickly and at scale, but it was never designed to be secure.
In simple terms, BGP works by enabling the edge routers of these autonomous systems (e.g. BT, Sky, Virgin Media, etc.) to share information about their available telecoms paths, network latency, and hop counts to establish the most efficient route for data transmission at any given time.
If a route changes for any reason (and they very often do), the routers responsible for those routes quickly inform their neighbour routers of the changes in the network to allow those routers to make informed decisions about how they might need to re-route traffic to avoid the old route, or even to prefer a new route.
These network change messages can be sent either “upstream” to other networks using eBGP (External BGP), or “downstream” to those networks the AS is responsible for via iBGP (Internal BGP) announcements.
These announcements are sent based on the AS routing policy. An AS routing policy is a list of the IP address space that the AS controls, plus a list of the other ASes to which it connects.
The problem
BGP lacks a native way to verify that a network actually owns the addresses it claims to (it cannot verify the policies). As such it is highly vulnerable to route hijacks, route leaks, and nation-state weaponisation such as route manipulation and black-holing routes
A great example of such an Incident happening with a BGP route hijack is the 2008 incident between Pakistan Telecoms and Youtube where an engineer at the Pakistani network accidentally issued an eBGP announcement to the Internet instead of an iBGP announcement to their customers. the effect of this mistake was to route the whole of YouTube’s data into Pakistan for over an hour. This incident is visualised in this video (ironically hosted on Youtube). A case study of this incident is also available to read here
Whilst the YouTube-Pakistan incident was an accident, the number of BGP attacks which happen deliberately is huge – this infographic from Anapaya shows some of the biggest BGP hijacks over the last 10 years, and the impact they have had on many organisations across the globe.
Patches to BGP such as Resource Public Key Infrastructure (RPKI) and BGPsec have been layered on top of the original protocol to try to limit such events from happening, they only help at the margins of the networks – they fail to solve the underlying problems.
Cloudflare and other experts warn that despite improvements to BGP security in recent years, such as RPKI, only about 6.5% of Internet users are fully protected by Route Origin Validation (ROV), leaving the network open to stealthy, targeted hijacks.
Enter SCION
Adrian Perrig, a professor of computer science at ETH Zürich states that “the current state of internet security is like a boat full of holes: we keep patching the gaps and bailing out water, but the hull remains compromised”
To fix this, Perrig has spent the last 11 years developing a fundamental redesign of internet routing architecture known as SCION (Scalability, Control, and Isolation On Next-Generation Networks).
Full documentation about the aims os SCION, and how to implement the protocol can be found here
How SCION Changes the Game
SCION aims to replaces the Internet’s foundation entirely, providing genuine senders and receivers control over their data’s path. It achieves this through three interlocking mechanisms:
- Multi-path routing: Instead of a single path between two points, SCION establishes tens or hundreds of parallel paths. If one fails, the system reroutes within milliseconds—so fast that the human brain cannot even process the outage.
- Isolation Domains (ISDs): SCION allows regions, countries, or organizations to define their own local trust roots, eliminating the need to rely on a massive global ecosystem of certificate authorities. This makes cascading global failures like the configuration error in Australia that took down ATMs across Europe structurally impossible.
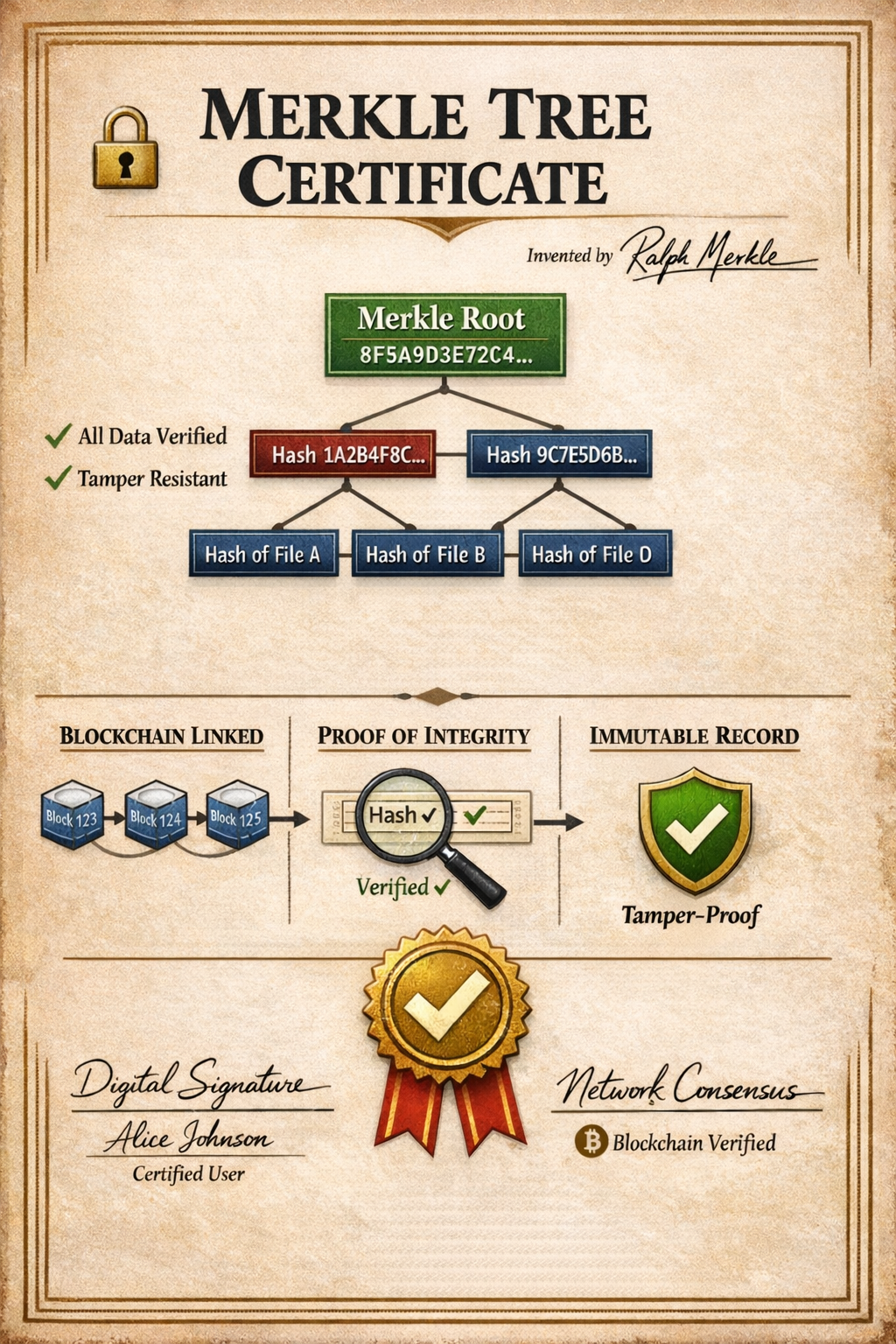
- Cryptographic path validation: Every router along a SCION path must provide a cryptographic signature, ensuring that packets cannot be secretly rerouted through unauthorised networks.
Proven in the real world
SCION isn’t just an academic theory; it is currently powering the Swiss financial system. In 2019, SIX Group (operator of the Swiss Stock Exchange and interbank payment infrastructure) partnered with the Swiss National Bank to build the Secure Swiss Finance Network (SSFN) using SCION.
This network handles 220 billion Swiss francs in daily interbank clearing. During a carrier shutdown test, the failover was so seamless (under one millisecond) that the engineering team didn’t even notice the underlying network topology had changed. As a result, the older 20-year-old (Multi-Protocol Label Switching) MPLS infrastructure is actively being phased out in favor of SCION.
Why isn’t it everywhere?
Despite its success in Switzerland, SCION has struggled to gain global traction for a few key reasons:
- Lack of Standardization: BGP is an official IETF standard, whereas SCION currently only has an Independent Stream RFC in progress. Large organisations are hesitant to deploy non-standardised protocols due to the risk of diverging implementations or costly future changes.
- The “Chicken-and-Egg” Dilemma: The pain of traditional BGP networks—latency spikes and three-minute failovers—is known and tolerated. Organizations have adapted to it and are generally numb to the advantages of a new system.
- Vendor Concentration: Currently, a single ETH Zürich spin-off called Anapaya offers the only commercial implementation. Major networking giants like Cisco are waiting for SCION to become a massive multibillion-dollar market before jumping in, but the market can’t reach that size without their participation
- The Psychology of Infrastructure: Replacing a fundamentally flawed but currently functioning internet architecture is a nearly impossible pitch to corporate boards
The future of Internet routing
SCION is increasingly being discussed in the context of European “digital sovereignty” because its isolation domains allow countries to operate independently of US-based certificate authorities and resist central kill switches. However this same level of control could theoretically be weaponised by totalitarian governments to restrict a free Internet.
Perrig remains highly optimistic, predicting that SCION will be embedded in core network libraries within three to five year. But cybersecurity professor Kevin Curran offers a more sobering prediction: true global adoption likely won’t happen incrementally. Instead, it will require a sufficiently dramatic failure of the existing internet infrastructure such as a major state-sponsored attack taking down national infrastructure to finally force the world to upgrade its 40-year-old foundation technology.