Coruna: A very powerful iOS exploit kit
Google’s Threat Intelligence Group (GTIG) has uncovered a massive new iOS exploit kit dubbed “Coruna”. The malware targets Apple iPhone models running iOS 13.0 through to iOS 17.2.1, Coruna is a formidable threat armed with 23 distinct exploits and five complete exploit chains.
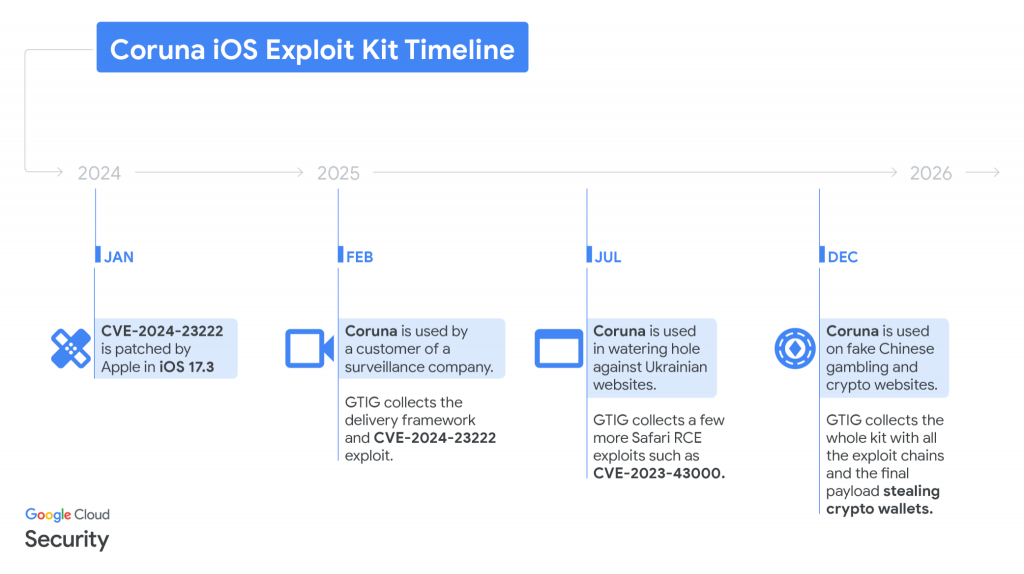
A Timeline of Proliferation
- February 2025: GTIG first identified fragments of the exploit chain being utilised in highly targeted operations by a customer of a commercial surveillance vendor (The malware is widely believed to have been developed for the US government). The exploits were wrapped in a unique JavaScript framework designed to fingerprint devices.
- Summer 2025: The kit then resurfaced in the hands of UNC6353, a suspected Russian espionage group. They deployed Coruna in watering hole attacks targeting Ukrainian users, hiding the malicious framework within compromised local websites ranging from retail tools to industrial equipment.
- Late 2025: Finally, the complete exploit kit was acquired by UNC6691, a financially motivated threat actor operating out of China. This group deployed Coruna on a massive scale, using hidden iFrames injected into fake cryptocurrency exchange websites to trap unsuspecting victims.
Under the Bonnet
The framework driving Coruna is exceptionally well-engineered. When a user visits a compromised site, the kit actively fingerprints the device and will immediately halt the attack if it detects the user is in Private Browsing mode or is using Apple’s Lockdown mode.
If the device is vulnerable, the malware delivers unencrypted Remote Code Execution (RCE) and Pointer Authentication Code (PAC) bypasses. It then deploys a binary loader that pulls down heavily obfuscated payloads that are encrypted with the ChaCha20 encryption algorithm. The malware is compressed and tailored specifically to the target’s iOS version and internal chipset. Notably, the threat actors utilised powerful vulnerabilities, including CVE-2024-23222, a zero-day vulnerability which was patched by Apple in January 2024.
As mentioned above, the malware utilises 23 exploits to bypass device security, evade discovery, elevate privilege levels, and maintain persistence
| Type | Codename | Targeted versions (inclusive) | Fixed version | CVE |
| WebContent R/W | buffout | 13 → 15.1.1 | 15.2 | CVE-2021-30952 |
| WebContent R/W | jacurutu | 15.2 → 15.5 | 15.6 | CVE-2022-48503 |
| WebContent R/W | bluebird | 15.6 → 16.1.2 | 16.2 | No CVE |
| WebContent R/W | terrorbird | 16.2 → 16.5.1 | 16.6 | CVE-2023-43000 |
| WebContent R/W | cassowary | 16.6 → 17.2.1 | 16.7.5, 17.3 | CVE-2024-23222 |
| WebContent PAC bypass | breezy | 13 → 14.x | ? | No CVE |
| WebContent PAC bypass | breezy15 | 15 → 16.2 | ? | No CVE |
| WebContent PAC bypass | seedbell | 16.3 → 16.5.1 | ? | No CVE |
| WebContent PAC bypass | seedbell_16_6 | 16.6 → 16.7.12 | ? | No CVE |
| WebContent PAC bypass | seedbell_17 | 17 → 17.2.1 | ? | No CVE |
| WebContent sandbox escape | IronLoader | 16.0 → 16.3.116.4.0 (<= A12) | 15.7.8, 16.5 | CVE-2023-32409 |
| WebContent sandbox escape | NeuronLoader | 16.4.0 → 16.6.1 (A13-A16) | 17.0 | No CVE |
| PE | Neutron | 13.X | 14.2 | CVE-2020-27932 |
| PE (infoleak) | Dynamo | 13.X | 14.2 | CVE-2020-27950 |
| PE | Pendulum | 14 → 14.4.x | 14.7 | No CVE |
| PE | Photon | 14.5 → 15.7.6 | 15.7.7, 16.5.1 | CVE-2023-32434 |
| PE | Parallax | 16.4 → 16.7 | 17.0 | CVE-2023-41974 |
| PE | Gruber | 15.2 → 17.2.1 | 16.7.6, 17.3 | No CVE |
| PPL Bypass | Quark | 13.X | 14.5 | No CVE |
| PPL Bypass | Gallium | 14.x | 15.7.8, 16.6 | CVE-2023-38606 |
| PPL Bypass | Carbone | 15.0 → 16.7.6 | 17.0 | No CVE |
| PPL Bypass | Sparrow | 17.0 → 17.3 | 16.7.6, 17.4 | CVE-2024-23225 |
| PPL Bypass | Rocket | 17.1 → 17.4 | 16.7.8, 17.5 | CVE-2024-23296 |
Despite its origins in the surveillance sector, Coruna’s final payload is strictly financial. Tracked by GTIG as PLASMAGRID, the stager binary injects itself into a root-level iOS daemon with its primary goal being cryptocurrency theft.
The payload is capable of decoding QR codes from saved images and scanning Apple Memos for word sequences or specific keywords like “bank account” and “backup phrase”. The malware also remotely downloads modules designed specifically to hook into and exfiltrate data from popular crypto wallets, including MetaMask, Trust Wallet, and Exodus.
According to GTIG, the developers of the malware left behind internal logs written in Chinese, with some code comments featuring emojis and syntax suggesting they may have been generated by an LLM. The malware also uses a custom domain generation algorithm (DGA) seeded with the word “lazarus” as a fallback mechanism to maintain contact with its command and control servers.
How to Protect Your Device
Google has shared its research to raise industry awareness and has already added all identified malicious domains to Safe Browsing to safeguard users.
Because the Coruna exploit kit relies on older vulnerabilities and is not effective against the latest Apple software, the absolute most effective defence is to update your iPhone to the latest version of iOS. For those users who are unable to update their devices for any reason, enabling Apple’s Lockdown Mode is strongly recommended, as the exploit kit is programmed to automatically bail out when this enhanced security feature is active.