SMS scammers sentenced
A British Transport Police (BTP) investigation has resulted in four men being sentenced to jail for their parts in a sophisticated scam that involved SMS blasters, tricking people into divulging personal data that was then used in multiple fraudulent activities. A fifth gang-member is currently on the run.

Wan Mohd Hafiz (left), Zhijia Fan (Centre), and Daoyan Shang (right) were sentenced at Inner London Crown Court on the 24th February 2026
Hafiz received a sentence of one year for conspiracy to defraud, and a further 2 months for possession of articles for use in fraud. Fan (the gang ring-leader) was sentenced to four years and eight months, for conspiracy to defraud, and Shang was jailed for two years and ten months for his part in the scam.
The fourth man arrested (Gatis Lauks) was given a sentence of two years suspended for two years for pleading guilty to fraud by misrepresentation.
The fifth gang member (Jinhua Zhang) fled after being released on police bail.
The investigation into the gang was launched back in March 2025 when an off-duty British Transport Police (BTP) detective spotted a man sitting at a platform at King’s Cross Underground station with a suitcase containing holes that was emitting a green flash.
The detective alerted BTP officers in the station to the suspicious item and they quickly responded to detain the man.
On examination of the suitcase, an SMS blaster was discovered inside The Blaster is a device that masquerades as a legitimate mobile cell tower and tricks nearby phones to connect to it. Once phones are connected to it, the device sends mass messages with links to fraudulent websites.

Two weeks later, a second SMS blaster was seized from Hafiz when BTP officers in plain clothes detained him at Baker Street Underground station. He had been sitting on the platform with the device, again concealed inside a large suitcase.
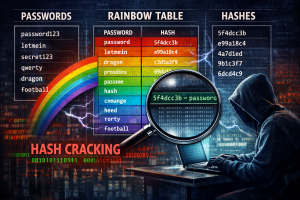
These devices were found to be sending messages to Tube passengers’ phones purporting to be from Royal Mail and Evri. The messages stated that a package could not be delivered to the users address, and contained links which people were tricked into entering personal details. These details allowed the scammers to access the victims bank accounts and extract money. The details were also used to commit acts of fraud by allowing the gang to create fake accounts to purchase goods.
The intelligence developed by BTP detectives uncovered Fan and Shang as the pair orchestrating the fraud conspiracy.
Raids on the addresses of the gang members uncovered key components used to build the SMS blasters, including antennas and power units. Also seized from the addresses were 10,832 gift cards loaded with over £80,000 in profits generated from their fraudulent activities.
A statement from Jonathan Kelleher from the Crown Prosecution Service said that “While Fan maintained a physical distance, Daoyan Shang would accompany the SMS blasters, a portable and an illegal device used to impersonate a legitimate cellular tower and forcing nearby mobile phones to connect, onto the Underground and provide technical support in case they malfunctioned.”
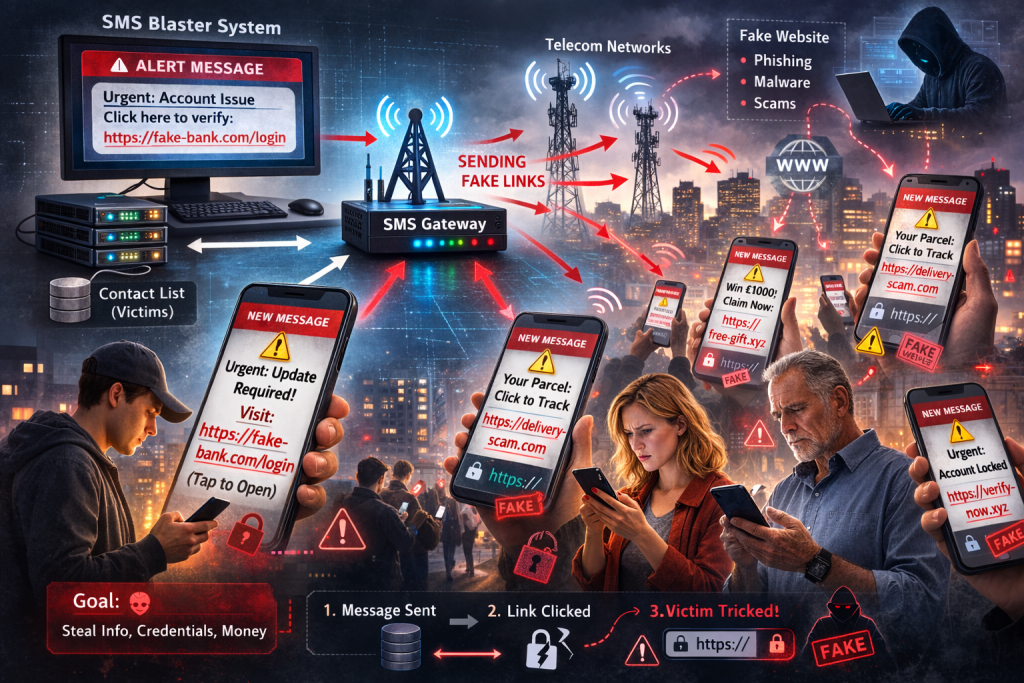
How does an SMS blaster work?
An SMS blaster (A.K.A. bulk SMS sender) is a system that sends a single message to many phones by passing it from a web/app interface to an SMS gateway then to numerous mobile networks to be passed to recipients’ devices.
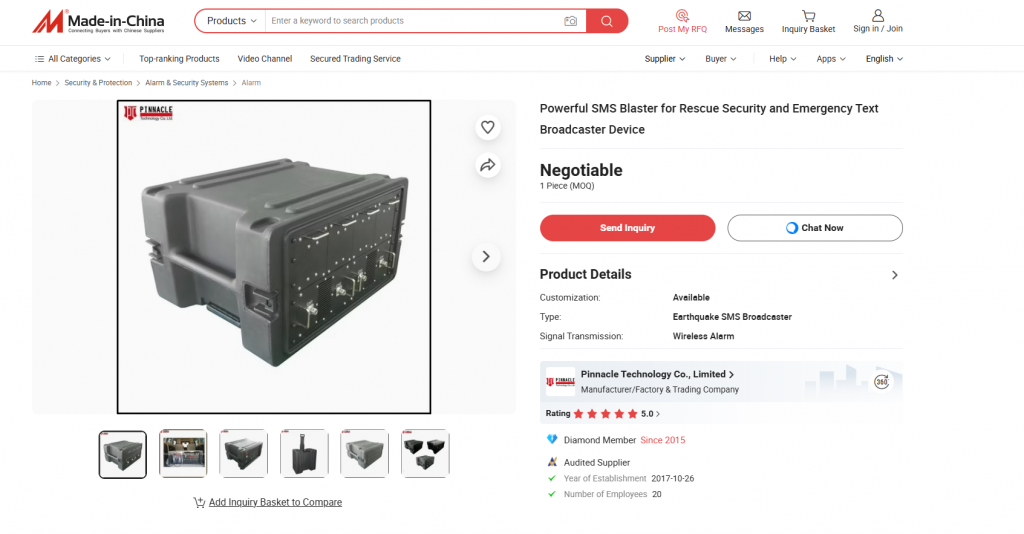
In some parts of the world, such devices are perfectly legal – but in the UK, they are not. For example, the one shown in the image below is used by emergency services to alert people in times of natural disasters when the normal mobile network is disrupted. The device is used to send warning messages to mobile devices in range, so that users can get to safety in events such as floods, or wildfires.

In this case, the blasters used in this scam were used to drown-out legitimate mobile signals, and trick devices to connect to them instead of real mobile towers. This allowed the gang to target all users within range of the device to send the messages as if they were coming from legitimate sources.