What is gopherware?
Gopherware (Gopher malware) is the term given to malware written in the Go (Golang) programming language. As a threat, gopherware has seen a massive surge in adoption by threat actors since early 2019
Its popularity is driven by its ability to easily create cross-platform, self-contained binaries that are difficult to analyse and detect
Multiple malware variants written in Go are now live, some examples include:
Ekans – this is a Go-written ransomware strain that specifically targets OT / ICS systems. Named after the Pokemon character, Ekans was first observed in early 2020, and infects Windows systems. The malware has an embedded “kill list” that stops a wide range of Anti-malware processes as well as many processes and services for different Industrial Control Systems. After killing the processes, Ekans proceeds to delete all shadow copies to disable any restoration capabilities before running its encryption process.
eCh0raix is another example of a Go-written ransomware tool. This malware has been reported to affect QNAP NAS devices, and devices using weak passwords or outdated QTS firmware may be susceptible to compromise. First observed in 2021, this malware targets devices with a brute-force attack to gain access before deploying its encryption payloads. Researches have identified that the encryption keys are unique for each victim, making decryption for multiple victims almost impossible.
Skuld is a Go-written Info-stealer, first seen in May 2023. This malware searches for data stored in applications such as Discord and web browsers. Some analysed samples have included a module to steal cryptocurrency assets from victims.
Before stealing data, the malware checks if it is being analysed by a security product or researcher, via different properties of the environment (CPU behaviours, Network connectivity, Screen resolution, Registry artifacts, available memory, etc.). If the binary confirms this analysis, execution will terminate.
What is Golang?
To see why threat actors are turning more to Go for their malware, it helps to understand what Go is.
Go is an open-source programming language created by engineers at Google in 2009, to solve common problems developers faced with large-scale software systems, especially performance, concurrency, and code maintainability.
Key features of Go
Fast and Efficient
- Compiles directly to machine code (like C/C++)
- Very fast execution speed compared to other languages
- Efficient memory usage
Simple and Easy to Learn
- Clean, minimal syntax
- Small standard library with powerful built-in tools
Built-in Concurrency
- Uses lightweight threads (called goroutines) which run independently to other running functions
- Thousands of goroutines can execute simultaneously
- Channels make it easy to communicate between concurrent tasks
Strong Standard Library
- Built-in support for web servers, networking, file handling, cryptography, and more
Cross-Platform
- Works on Windows, macOS, Linux, and mobile platforms
- Easy to compile apps for different systems
So why do threat actors use Go?
If we re-examine the features of Go (above) we can link these features to the reasons why threat actors are turning to writing their exploits and tools in Go.
Fast and Efficient
When compiled, Go produces self-contained executables that bundle everything they need to operate
That means, there are:
- No external dependencies to install – less likely to be detected
- Fewer compatibility issues – More stable code
- Easier delivery to victims
Reverse-engineering and analysis of the malware is made slightly harder because the compiled binaries can be larger and less familiar to analysts – As well as seeing new malware written in Go, researchers are also discovering ages-old malware re-written in Go to avoid detection by traditional anti-malware solutions
Simple and Easy to Learn
Compared to other languages such as C and C++, Go is a relatively simple language to understand
These benefits include:
- Cleaner syntax – easier to learn and understand
- Memory management handled automatically – no need for creating complex memory-management routines
- Rich standard library – easy to build complex structures from reusable code
These features help lower the barrier for new malware authors.
Built-in Concurrency
The Goroutines make it easy to run many tasks in parallel with low processing overheads.
Malware can use this to:
- Scan networks quickly – less likely to be detected, and large networks can be enumerated easily
- Handle multiple victims
- Run background tasks without slowing down the host too much – less likely to raise suspicions
Strong Standard Library
Go has built-in libraries for many features desirable for threat actors:
- HTTP/HTTPS communication
- Sockets
- Concurrency (handling many connections at once)
These libraries are useful for malware features like:
- Command-and-control (C2) communication
- Data exfiltration
- Botnet coordination
Writing multiple features in traditional languages such as C and C++ etc. is complex, but relatively simple in Go. This enables malware writers to build complex capability with relative ease
Cross-Platform
As mentioned, Go is designed to compile for many operating systems from one codebase.
This means threat actors can write one program and quickly build versions for Windows, Linux, MacOS, Android, etc.
A lot of infrastructure today runs on Linux servers and containers, and Go is widely used in cloud software solutions. Go malware blends in better in those environments, making it harder to detect and remove such malware.
This makes Go ideal for malware campaigns targeting mixed environments.
In addition to the above mentioned features, because Go binaries look different from traditional malware written in C/C++, and often include lots of embedded libraries, some security tools historically had weaker detection heuristics for Go-based threats (though this has improved a lot in recent years).
So how do people detect Go malware?
System security defenders don’t rely on a single approach to identify and catch malware (Go or otherwise), but rather they have to take multiple approaches
Because Go programs are perfectly legitimate in many environments. a combination of static analysis, behavioural monitoring, memory forensics, and threat intelligence is used to identify suspicious Go binaries and activity.
Here’s how detection typically works:
Static analysis of the Go binary
Go executables have recognizable structural traits that analysts can inspect.
Some common indicators include:
- Go build metadata (version strings, module paths, build IDs)
- Large, statically linked binaries
- Function naming patterns (e.g.,
main.main, runtime packages) - Embedded Go standard library artifacts
Security tools and reverse-engineering frameworks (like Ghidra or IDA Pro) can parse these patterns and reconstruct function names and logic to make analysis easier.
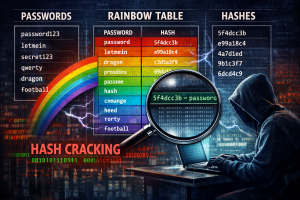
YARA rules and signature-based detection
YARA (Yet Another Ridiculous Acronym) was originally developed by Victor Alvarez of VirusTotal and was released on GitHub in 2013. It provides a rule-based approach to create descriptions of malware families based on regular expression, textual or binary patterns.
In 2024, Alvarez announced that YARA would be superseded by a rewrite called YARA-X, written in Rust. The first stable version of YARA-X was released in June 2025
YARA rules can be used to match patterns specific to Go malware families.
Examples of things rules look for:
- Strings tied to command-and-control domains
- Hardcoded encryption keys
- Known Go runtime markers
- Unique function or package names from a malware family
Even though Go binaries are big and noisy, they still contain distinct fingerprints which once identified can be detected by YARA rules.
Behavioural detection (EDR/XDR)
Modern security defences focus heavily on what a program does when executing, not just what it looks like. Suspicious behaviours might include:
- Unusual outbound connections (C2 beaconing)
- Dropping or modifying files in system directories
- Creating persistence (edited, or new registry keys, scheduled tasks, services)
- Capturing keystrokes or screenshots
- Spawning shells or running commands
Tools like Microsoft Defender for Endpoint can detect these actions regardless of the language used to write the malware.
The analysis of these heuristic behaviours can identify recognizable traffic patterns.
Some patterns to look for include:
- Beacon intervals (regular check-ins)
- Suspicious HTTP headers or user-agents
- TLS certificate anomalies
- Data exfiltration patterns
Network detection systems can flag these unusual communications even if the binary itself isn’t yet known.
Over time, researchers have learned patterns that are especially common in numerous malicious Go programs:
- Use of self-signed TLS certificates
- Embedded base64-encoded configs
- Hardcoded Telegram/Discord bot tokens for C2
- Anti-analysis tricks like checking mouse movement or CPU core activity/use
Memory forensics and runtime inspection
Even if a Go binary is packed or obfuscated, its runtime behaviour in memory can be analysed to see what it does
Forensic investigators will commonly look for:
- Loaded modules and strings in memory
- Decrypted payloads
- Suspicious threads or injected code
Forensics frameworks like Volatility help extract these artifacts.